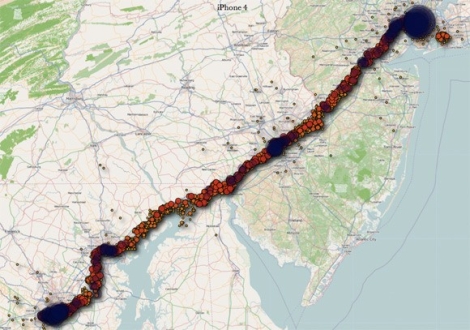
Last week, the Internet was alight with stories of iPhone location tracking. While this wasn’t exactly breaking news in security circles, it was new information to many people out there. Lots of blogs were full of commentary on the situation, including ours, with many Android users chiming in saying, “Android doesn’t do that”.
Well, that’s not entirely true – the playing field is far more level than most people would like to admit.
Android does have the same tracking capability, as do Windows Mobile phones for that matter. Both companies also monitor the cell towers you have connected to, as well as which Wi-Fi hotspots you have passed by. All three companies anonymize the data, though they do assign a unique ID to your location details in order to tell you apart from other users.
Where things really differ is in regards to how much information is stored. Microsoft claims that they only store the most recent location entry, while Andriod systems store the 200 most recent Wi-Fi hotspot locations as well as the most recent 50 cell towers.
At the end of the day each vendor does allow you to opt out of the tracking services, and if you are seriously concerned about the data they are tracking, you can always periodically wipe the information from your handset, should you desire.
[Image via TheTelecomBlog]