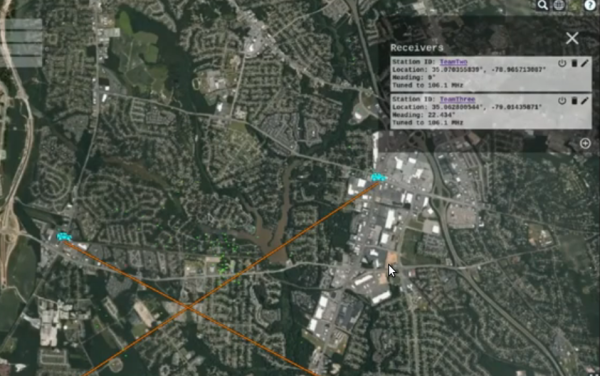
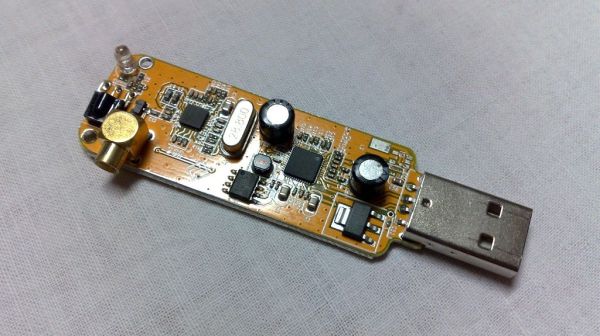
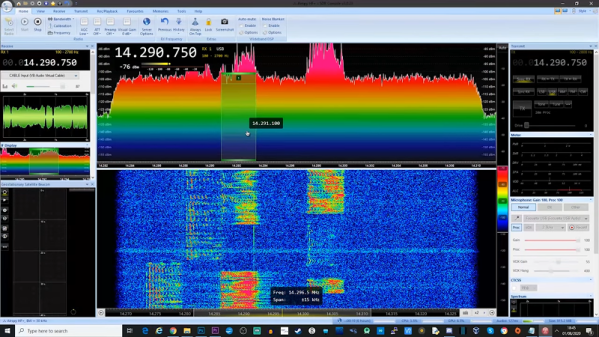
Fox hunting, or direction finding, is a favorite pastime in the ham radio community where radio operators attempt to triangulate the position of a radio transmission. While it may have required a large amount of expensive equipment in the past, like most ham radio operations the advent of software-defined radio (SDR) has helped revolutionize this aspect of the hobby as well. [Aaron] shows us how to make use of SDR for direction finding using his custom SDR-based Linux distribution called DragonOS.
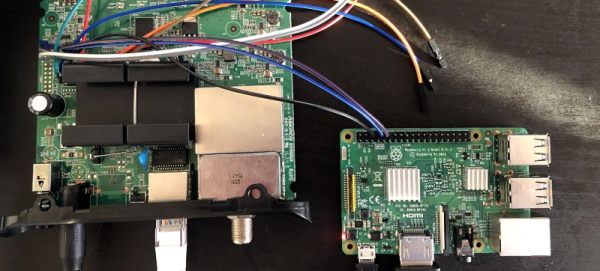
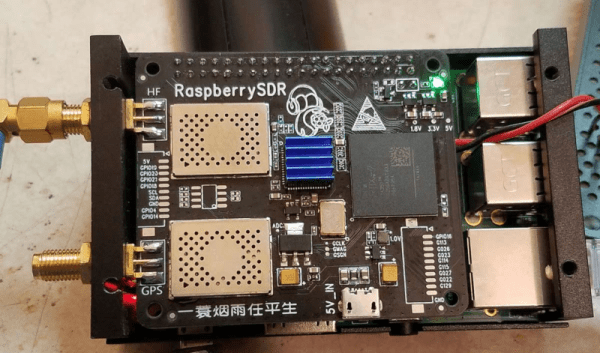
We have mentioned DragonOS before, but every iteration seems to add new features. This time it includes implementation of a software package called DF-Aggregator. The software (from [ckoval7]), along with the rest of DragonOS, is loaded onto a set of (typically at least three) networked Raspberry Pis. The networked computers can communicate information about the radio waves they receive, and make direction finding another capable feature found in this distribution.
[Aaron] has a few videos showing the process of setting this up and using it, and all of the software is available for attempting something like this on your own. While the future of ham radio as a hobby does remain in doubt, projects like this which bring classic ham activities to the SDR realm really go a long way to reviving it.