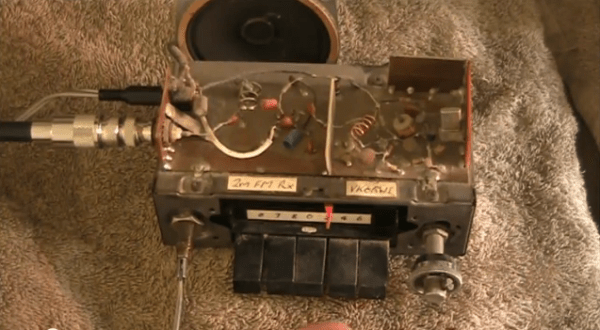
This amateur radio hack is not for the faint of heart! With only three transistors (and a drawer-full of passive parts), [Peter Parker, vk3ye] is able to use a broken-looking AM car radio to receive FM radio signals (YouTube link) on 2 meters, an entirely different band.
There are two things going on here. First, a home-made frequency downconverter shifts the 147 MHz signal down to the 1 MHz neighborhood where the AM radio can deal with it. Then, the AM radio is tuned just slightly off the right frequency and the FM signal is slope detected.
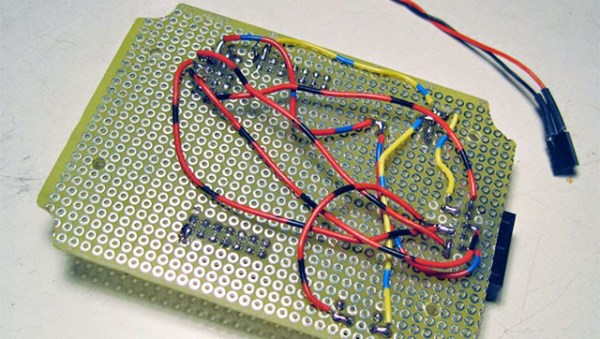
The downconverter consists of a local tuned oscillator and a mixer. The local oscillator generates an approximate 146 MHz signal from an 18 MHz crystal, accounting for two of the three transistors. Then this 146 MHz signal and the approximately 147 MHz signal that he wants to listen to are multiplied together (mixed) using the third transistor.
If you’re not up on your radio theory, a frequency mixer takes in two signals at different frequencies and produces an output signal that has various sums and differences of the two input signals in it. It’s this 147 MHz – 146 MHz = 1 MHz FM signal, right in the middle of the AM radio band’s frequency range, that’s passed on to the AM radio.
Next, the AM radio slope detects the frequency-modulated (FM) signal as if it were amplitude modulated (AM). This works as follows: FM radio encodes audio as changes in frequency, while AM radios encode the audio signal in the amplitude, or volume, of the radio signal. Instead of tracking the changing frequency as an FM radio would, slope detectors stick on a single frequency that’s tuned just slightly off from the FM carrier frequency. As the FM signal gets closer to or farther away from this fixed frequency, the received signal gets louder or quieter, and FM is detected as AM.
At 5:23, [vk3ye] steps through the circuit diagram. As he mentions, these are old tricks from circa 50 years ago, but it’s very nice to see a junk-box hack working so well with so few parts and receiving (very) high frequency FM on an old AM car radio. A circuit like this could make a versatile front end for an SDR setup. It makes us want to warm up the soldering iron.
Continue reading “Dusty Junk-bin Downconverter Receives FM On An AM Radio”