The chances are if you know someone who is a former Apple employee, you’ll have heard their Steve Jobs anecdote, and that it was rather unflattering to the Apple co-founder. I’ve certainly heard a few myself, and quick web search will reveal plenty more. There are enough of them that it’s very easy to conclude the guy was not a very pleasant person at all.
At the same time, he was a person whose public persona transcended reality, and his fan base treated him with an almost Messianic awe. For them everything he touched turned to gold, every new feature on an Apple product was his personal invention, every one of his actions even the not-so-clever ones were evidence of his genius, and anyone who hadn’t drunk the Apple Kool-Aid was anathema. You’ll still see echoes of this today in Apple fanboys, even though the shine on the company is perhaps now a little tarnished.
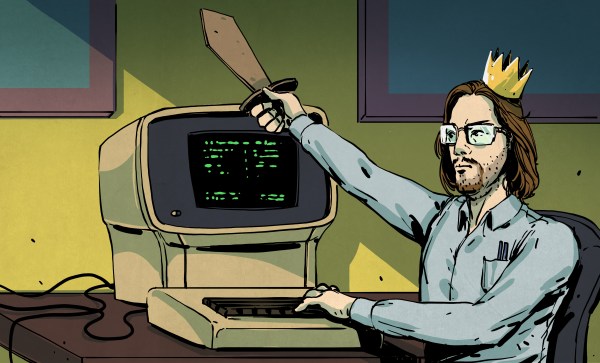
It’s easy to spot parallels to this story in some of today’s tech moguls who have gathered similar devotion, but it’s a phenomenon by no means limited to tech founders. Anywhere there is an organisation or group that is centred around an individual, from the smallest organisation upwards, it’s possible for it to enter an almost cult-like state in which the leader both accumulates too much power, and loses track of some of the responsibilities which go with it. If it’s a tech company or a bowls club we can shrug our shoulders and move to something else, but when it occurs in an open source project and a benevolent dictator figure goes rogue it has landed directly on our own doorstep as the open-source community. It’s happened several times that I can immediately think of and there are doubtless more cases I am unaware of, and every time I am left feeling that our community lacks an adequate mechanism to come through it unscathed. Continue reading “The Rogue Emperor, And What To Do About Them”