Computing goes hand-in-hand with how to structure and access data, and this internal training film from IBM regarding file organization and data processing with System/360 is from a time when such decisions were crucial to system architecture.
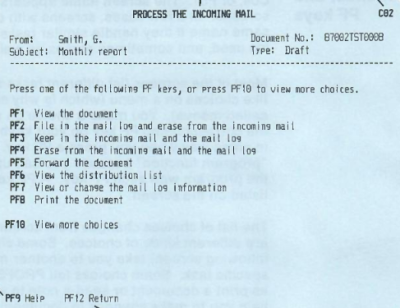
The presenter talks about the transition from magnetic tape-based storage (in which data is stored and must be read sequentially) to DASD (direct access storage devices) which have more in common with modern mass storage media. The ability to access and process data at will instead of sequentially represented a tremendous opportunity to change how organizations handled data. System/360 redefined mainframe computing, introducing not just the concept of compatibility and interoperability of programs and data between systems, but also popularized the 8-bit byte.
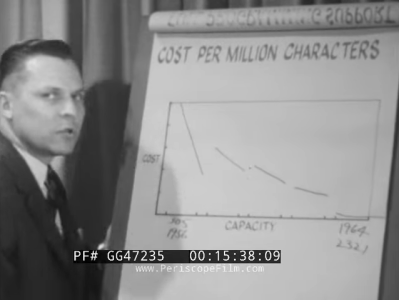
It’s not a particularly long presentation and it doesn’t go into deep technical detail — it was primarily aimed at sales people — but it does offer an interesting peek into a time period in computing history that most of us have little or no direct experience with. Nevertheless some things never change, like a trend of plummeting storage prices (listed as cost per million characters) over time.
Check it out in the video embedded below, and if you’d like to know more about IBM’s System/360 we have you covered.
Thanks [Stephen Walters] for the tip.
Continue reading “Peek Into IBM’s System/360 With Vintage Training Film”