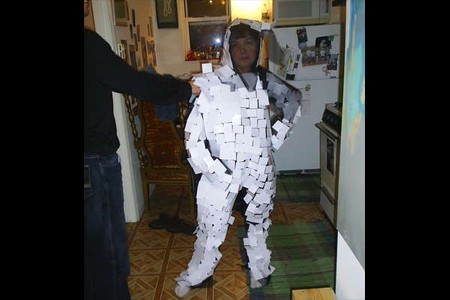
Though much of [citizenFinerran]’s intent in designing a suit that camouflages the wearer from security camera footage was philosophical, it is designed with a very tangible purpose in mind. The suit does not provide true camouflage (to say nothing of true invisibility), but it does create enough moving visual obstructions to make the wearer completely anonymous on film. More details on this and other invisibility cloaks after the break.
security474 Articles
Exploit-Me Firefox XSS And SQL Scanning Addon
[youtube=http://www.youtube.com/watch?v=RbL2ptbjoSA&hl=en&rel=0&color1=0x3a3a3a&color2=0x999999]
One of the best tools we saw at LayerOne was the Exploit-Me series presented by [Dan Sinclair]. Security Compass created these tools to help developers easily identify cross site scripting (XSS) and SQL injection vulnerabilities.
Continue reading “Exploit-Me Firefox XSS And SQL Scanning Addon”
How-To: Make An RGB Combination Door Lock (Part 1)

Part 2 can be found here
Putting a custom designed electronic lock on your space seems like a geek right of passage. For our latest workspace, we decided to skip the boring numbered keypad and build a custom RGB backlit keypad powered by an Arduino. Instead of typing in numbers, your password is a unique set of colors. In today’s How-To, we’ll show you how to build your own and give you the code to make it all work.
Continue reading “How-To: Make An RGB Combination Door Lock (Part 1)”
Bruce Schneier’s Opinion On Everything

Honestly, we were originally sent this Q&A with famed cryptographer [Bruce Schneier] as a restaurant recommendation (112 Eatery, Minneapolis). Posted last fall on NYTimes’ Freakonomics blog it covers [Bruce]’s opinion on nearly everything. Here are a few items in particular that really stuck out to us:
The most immediate threat to the average person is crime – in particular, fraud. And as I said before, even if you don’t store that data on your computer, someone else has it on theirs. But the long-term threat of loss of privacy is much greater, because it has the potential to change society for the worse.
What you’re really asking me is about the security. No one steals credit card numbers one-by-one, by eavesdropping on the Internet connection. They’re all stolen in blocks of a million by hacking the back-end database. It doesn’t matter if you bought something over the Internet, by phone, by mail, or in person – you’re equally vulnerable.
We already knew he doesn’t secure his WiFi (neither do we) and you’ll find many other interesting discussions in the article. If you want Bruce Schneier facts though, you’ll have to look elsewhere.
RFID Guardian V3 Released
[fbz] wanted to make sure that everyone knows that RFID Guardian has released the latest version of their design. I had a hard time finding a good shot of the hardware, so I went with the Nokia phone control application. There’s a short explanation of the project here. I’d point at the use examples on the site, but it seems that their MYSQL server is running out of memory. After seeing this talk at shmoocon last year, and a bit more reinforcement at defcon, there are definitely some good uses for the guardian. (Once you get past the slow start, Major’s intro is funny as hell. – jump past the first 8 minutes or you’ll be bored.)










