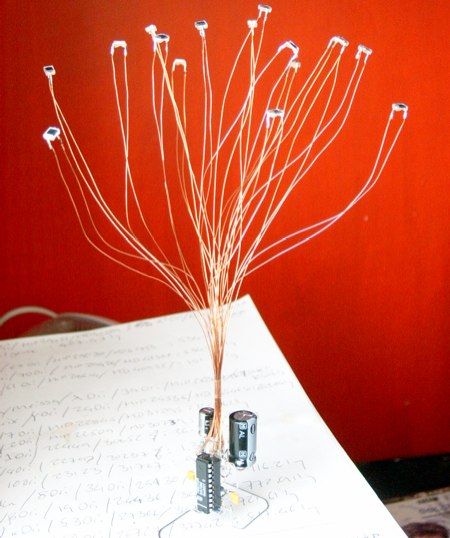
We spotted [Kerrin Mansfield]’s lovely solar engine on ladyada’s rantings. It uses 16 1/8th inch solar cells to collect power. At night, an orange LED pulses at .2Hz. He doesn’t have a specific write up on the construction, but from the component layout, it looks identical to [Gareth Branwyn]’s schematic in Make 08, which you can find in the PDF.
Day: June 14, 2008
RoboGames 2008 Photos And Videos

Laughing Squid’s [Scott Beale] is attending RoboGames 2008. Check out the great pictures and videos he took on Flickr.
Detecting ISP Throttling
ISPs have recently become very aggressive towards their customers. They’ve been blocking or altering traffic to prevent you from using specific programs or protocols. Google’s Senior Policy Director recently stated that they’re developing tools to allow people to detect ISP interference. A couple other groups have been building tools as well: The Network Neutrality Squad just released the second beta of their Network Measurement Agent. The tool currently detects spoofed packets by monitoring the round trip time of the connection; early reset packets will have lower than average RTT. If you want to go more in depth, the EFF has published a guide for using Wireshark to do the detection. We’ve even heard rumors of people building tools to tunnel a session inside of one that looks completely different.
[photo: nrkbeta]
PSP L2/R2 Button Mod

This is quickly becoming an unintentional “game controller Saturday”. We haven’t been covering the PSP much lately, so this is a treat. AcidMods forum member [Electro] put together a quick guide for adding two missing shoulder buttons to the PSP. The L2 and R2 buttons are used while playing Playstation 1 games and are usually mapped to directions on the joystick. This mod jumps the joystick’s contacts an relocates the buttons to the shoulders. The switches used in the post seem kind of bulky, but you’re free to use anything that fits.
[via Engadget]
X2Wii, NES/SNES/N64 To Wii Adapter

If you poke around [Raphaël]’s site, the creator of today’s featured hack, you’ll find a lot of interesting projects. X2Wii is an ongoing project to adapt controllers from earlier console generations so they work with the Wii’s GameCube ports. He adapted his Multiuse tiny1 which uses an ATmega8. The code is all assembly so the microcontroller can keep up with the protocol. Definitely check out [Raphaël]’s other project pages.
Universal Joystick USB Interface
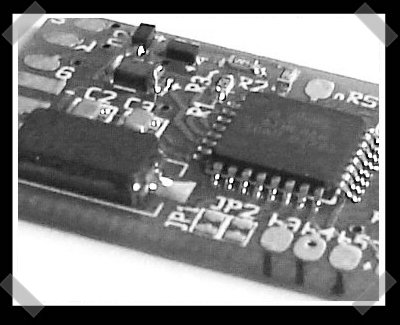
Building on his USB NES pad interface, [Raphaël] released a universal USB joystick interface. It presents a HID device with four directional buttons and eight general purpose buttons. The board uses an ATmega8 and implements USB entirely in software.
Exploit-Me Firefox XSS And SQL Scanning Addon
[youtube=http://www.youtube.com/watch?v=RbL2ptbjoSA&hl=en&rel=0&color1=0x3a3a3a&color2=0x999999]
One of the best tools we saw at LayerOne was the Exploit-Me series presented by [Dan Sinclair]. Security Compass created these tools to help developers easily identify cross site scripting (XSS) and SQL injection vulnerabilities.
Continue reading “Exploit-Me Firefox XSS And SQL Scanning Addon”










