You might think that a nuclear explosion is not something you need a detector for, but clearly not everyone agrees. [Bigcrimping] has not only built one, the BhangmeterV2, but he has its output publicly posted at hasanukegoneoff.com, in case you can’t go through your day without checking if someone has nuked Wiltshire.
The Bhangmeter is based on an off-the-shelf “nuclear event detector”, the HSN-1000L by Power Device Corporation.
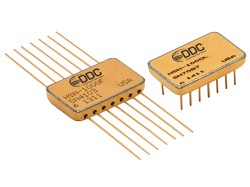
Interfacing to the HSN-1000L is very easy: you give it power, and it gives you a pin that stays HIGH unless it detects the characteristic gamma ray pulse of a nuclear event. The gamma ray pulse occurs at the beginning of a “nuclear event” precedes the EMP by some microseconds, and the blast wave by perhaps many seconds, so the HSN-1000 series seems be aimed at triggering an automatic shutdown that might help preserve electronics in the event of a nuclear exchange.
[Bigcrimping] has wired the HSN-1000L to a Raspberry Pi Pico 2 W to create the BhangmeterV2. In the event of a nuclear explosion, it will log the time the nuclear event detector’s pin goes low, and the JSON log is pushed to the cloud, hopefully to a remote server that won’t be vaporized or bricked-by-EMP along with the BhangmeterV2. Since it is only detecting the gamma ray pulse, the BhangmeterV2 is only sensitive to nuclear events within line-of-sight, which is really not where you want to be relative to a nuclear event. Perhaps V3 will include other detection methods– maybe even a 3D-printed neutrino detector?
If you survive the blast this project is designed to detect, you might need a radiation detector to deal with the fallout. For identifying exactly what radionuclide contamination is present, you might want a gamma-ray spectrometer.
It’s a sad comment on the modern world that this hack feels both cold-war vintage and relevant again today. Thanks to [Tom] for the tip; if you have any projects you want to share, we’d love to hear from you whether they’d help us survive nuclear war or not.