The art of the electronic conference badge has evolved over the last decade or more, such that for an individual example to be of note it now has to include some exceptional features. Perhaps a function that might previously have been considered impossible in a badge, or maybe an unusually beautiful design, an entertaining and compelling functionality, or it simply pushes the capabilities of an otherwise limited device in an unusually ingenious way. The badge from the recent Hacker Hotel 2020 comes from the same badge team that created the software platform derived from the SHA 2017 badge, and it ticks many of these boxes by combining a genuine work of art with a set of delightfully intricate puzzles at enough levels to interest all participants in the event.
badge158 Articles
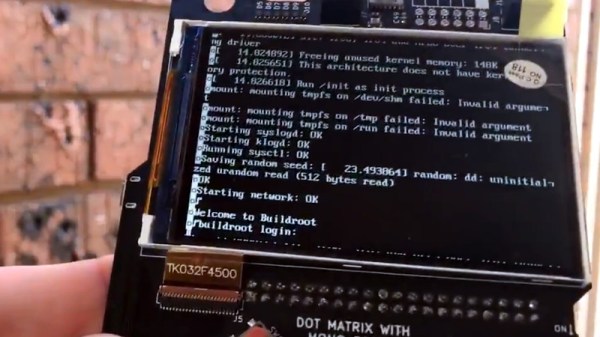
Watch Linux Boot On Your Hackaday Superconference Badge
Last year’s Hackaday Superconference badge was an electronic tour de force, packing an ECP5 FPGA shoehorned into a Game Boy-like form factor and shipping with a RISC-V core installed that together gave an almost infinite badge hacking potential. It did not however run Linux, and that’s something [Greg Davill] has addressed, as he’s not only running Linux on his badge, but also a framebuffer that allows him to use the badge screen as the Linux terminal screen. Finally you can watch Linux boot on your Superconference badge itself, rather than over its serial port.
He’s achieved this by changing essentially everything: from the new VexRiscv CPU core, to new video drivers and a VGA terminal courtesy of Frank Buss, now part of the LiteVideo project. It’s not quite a fully fledged Linux powerhouse yet, but you can find it in a GitHub repository should you have a mind to try it yourself. Paging back through his Twitter feed reveals the effort he’s put into this work over the last few months, and shows that it’s been no easy task.
For those keeping score at home, this is an open hardware design, running an open CPU core, with community-designed open-source peripherals, compiled by an open-source toolchain, running an open-source operating system. And it’s simply a fantastic demo for the badge, showing off how flexible the entire system is. One of the best parts of writing for Hackaday is that our community is capable of a huge breadth of amazing pieces of work, and this is an exemplar of that energy. We can’t wait to see what Greg and any other readers tempted to try it will come up with.
If you’d like to refresh your memory over the 2019 Supercon badge, here’s our write-up at the time.
Developing Retro Games For Conference Badges With Kate Morris
PCB badges have exploded in popularity in recent years. Starting out as a fun token of entry to a conference, they’re now being developed by all manner of independent groups, with DEFCON serving as the heart of the #badgelife movement. After DEFCON 26, Kate Morris and associates decided to undertake the development of their own badge, to celebrate the 50th anniversary of the Apollo landing. Kate’s talk at the 2019 Hackaday Superconference serves to tell the tale of creating a retro game to run on a badge platform.
Continue reading “Developing Retro Games For Conference Badges With Kate Morris”
Machine Inside Of A Chip: How Sprite_TM Built The FPGA Game Boy Badge
Kids of the 1990’s would call you a liar if you told them that within thirty years you’d go to a conference and be handed a Super Nintendo Entertainment System to wear around your neck. But that’s what happened with the badge Jeroen Domburg, aka [Sprite_TM], designed for the 2019 Hackaday Superconference. It’s built in the Game Boy form factor, complete with a cartridge slot, beautiful screen, and the familiar button layout. But there’s so much more here, like the HDMI port on the bottom and the ability to completely reconfigure the device by dropping a binary file onto it over USB.
Of course what makes this possible is the FPGA at the heart of the design. The story of how the badge was developed is shared in great detail during Sprite’s Supercon talk. The timeline, the hardware choices, and the oopses along the way make for a great story. But what you really don’t want to miss is how he built the machine inside of the FPGA — the collection of Verilog code known as “gateware” that brings together the System-on-a-Chip (SoC). From his delight at being able to spawn more processor cores by changing a single variable, to the fascinating SNES-inspired graphics subsystem, the inside story shared below is even more interesting than the physical device itself.
Continue reading “Machine Inside Of A Chip: How Sprite_TM Built The FPGA Game Boy Badge”
Star Wars Themed Laser Badge: All That Is Missing Is The Pew Pew Sound Effect
In the quest to advance the art of the electronic badge, the boundaries of what is possible to manufacture in small quantities are continually tested. Full-colour PCBs, injection moulding, custom keyboards, and other wow factor techniques have all been tried, leading to some extremely impressive creations. With all this innovation then it’s sometimes easy to forget that clever design and a really good idea can produce an exceptional badge with far more mundane materials.
The 10th InCTF cybersecurity contest held at Amrita, Kerala, India, had a Star Wars themed badge designed by Team bi0s for the event. It takes the form of a Millennium Falcon-shaped PCB, with a NodeMCU ESP8266 board mounted on it, a shift register, small OLED display, and the usual array of buttons and LEDs. The fun doesn’t stop there though, because it also packs a light-dependent resistor and a laser pointer diode that forms part of one of its games. Power for this ensemble comes courtesy of a set of AA cells on its underside.
They took a novel approach to the badge’s firmware, with a range of different firmwares for different functions instead of all functions contained in one. These could be loaded through means of a web-based OTA updater. Aside from a firmware for serial exploits there was an Asteroids game, a Conway’s Game Of Life, and for us the star of the show: a Millennium Cannon laser-tag game using that laser. With this, attendees could “shoot” others’ LDRs, with three “hits” putting their opponent’s badge out of action for a couple of minutes.
Unusually this badge is a through-hole design as a soldering teaching aid, but its aesthetics do not suffer for that. We like its design and we especially like the laser game, we look forward to whatever next Team bi0s produce in the way of badges.
This isn’t the first badge packing a laser we’ve seen, at last year’s Def Con there was a laser synth badge. No laser tag battles though.
Add A Bit Of PCB Badge Glamour To Your Boring ID Badge
When we talk about badges and printed circuit boards, it is usually in the context of the infinite creativity of the Badgelife scene, our community’s own art form of electronic conference badges. It’s easy to forget when homing in on those badges that there are other types of badge, and thus [Saimon]’s PCB badge holder is an entertaining deviation from our norm. His workplace requires employees to carry their credit-card-sized ID pass with them at all times, but the plastic holder that came with his had broken. So he did what any self-respecting engineer would do, and designed his own holder using PCBs.
It’s a three-way sandwich with identical front and back PCBs featuring a nice design, but the clever bit is the middle PCB. It is U-shaped to slide the card in from the side, but to retain the card it has a couple of springy milled PCB arms each with a small retaining tooth on the end. This is an ingenious solution, with just enough give to bend, but not so much as to break.
The three boards are glued together, it seems his original aim was to reflow solder them but this was not successful. The result is an attractive and functional badge holder, which if Hackaday required us to have a corporate ID you can be sure we’d be eyeing up for ourselves.
Behind The Scenes Of The 2019 Superconference Badge
If you count yourself among the several hundred of our closest friends that have joined us at Supplyframe HQ for the 2019 Hackaday Superconference, then by now you’ll have your hands on one of this year’s incredible FPGA badges. It should come as no surprise that an incredible amount of time and effort went into developing and manufacturing this exceptionally unique piece of hardware; the slick gadget in your hands today took nearly an entire year to develop, and work continued on it until very literally the last possible moment.
 Badge designer Jeroen Domburg (aka Sprite_TM), Hackaday staff, and a team of dedicated volunteers were still putting the final touches on these ambitious devices less than 24 hours before they were distributed to the first wave of Superconference attendees. Naturally, that’s not exactly how things were supposed to go. But when you’ve got a group of people that want to push the envelope and build something truly incredible, convincing them to actually stop working can be a challenge in itself.
Badge designer Jeroen Domburg (aka Sprite_TM), Hackaday staff, and a team of dedicated volunteers were still putting the final touches on these ambitious devices less than 24 hours before they were distributed to the first wave of Superconference attendees. Naturally, that’s not exactly how things were supposed to go. But when you’ve got a group of people that want to push the envelope and build something truly incredible, convincing them to actually stop working can be a challenge in itself.
In fact, development of the badge is still ongoing. Fixes and improvements are being made to the software even as you read this, and if you haven’t already, you should upgrade your badge to make sure you’ve got the latest and greatest from our international team of wizards. We all know that conference badges have an unfortunate habit of languishing on the shelf and collecting dust, but the 2019 Superconference badge was built to challenge you for longer than just one weekend. Consider yourself warned: for every Supercon badge that gets tossed in a drawer come Monday, Sprite_TM will shed a single tear.
After the break, come along as we turn back the clock and take a look at the last minute dash to get 500+ badges programmed and ready to go before the doors opened for the 2019 Hackaday Superconference.
Continue reading “Behind The Scenes Of The 2019 Superconference Badge”