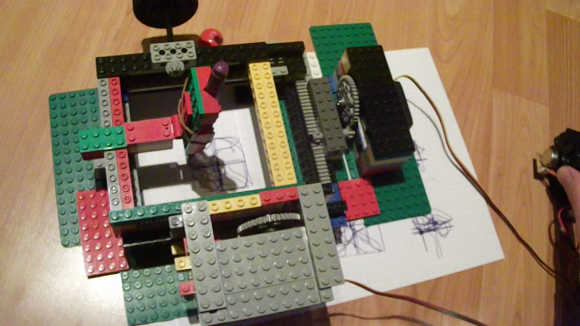
Loving to draw but deathly afraid of pen ink, [Marcel] came up with a little drawing machine made out of Lego that will do it for him. It’s not a very complicated build but it does have several different components arranged such to complete a task, and that in itself is cool. Oh yeah, just kidding about the “afraid of pen ink” thing.
RC Car Servos are used to drive the pen in the X and Y directions. These servos only have a 180 degree range of motion which is not enough to move the pen very far. To increase the pen’s travel distance, [Marcel] attached a large gear to the servo which rotates a much smaller gear that rides on a rack gear attached to the bed. A Lego hinge takes the place of a Z axis and is used to set the height of the pen that is strapped to the machine via rubber band.
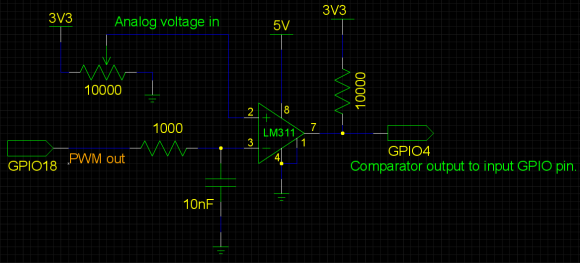
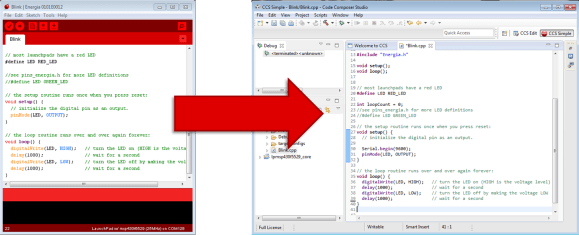
In order to make the machine draw, the user moves an analog joystick. The changing resistance values of the joystick’s potentiometers are measured by an Arduino. The Arduino then moves each servo to the appropriate position using PWM. If you’d like to know how to do this, check out the Knob Tutorial.
If you’re not ready to l’eggo your Lego drawing machines, check out this super complicated creation or this arm emulator that draws the Mona Lisa.