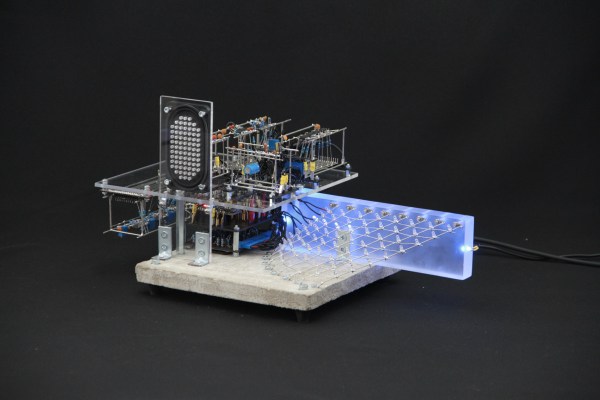
The quest for true randomness has roots in cryptography and is a rabbit hole that gets surprisingly deep with alarmingly rapidity. Still, the generation of random-enough numbers is a popular hacker project. Part of the appeal is the way these devices strive to incorporate physical phenomena, and in [Joshua Coleman]’s case, his Neon Entropy (Pseudo) Random Number Generator uses a trio of vintage neon lamps.
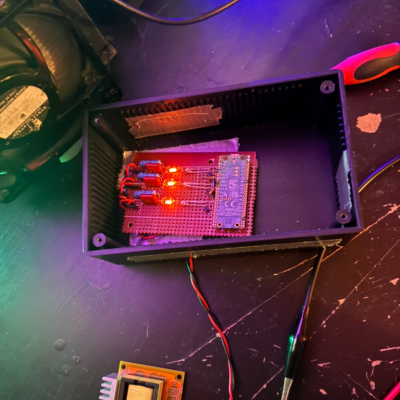
[Joshua] chose neon lamps in part because the discharge rate of an energized lamp is a variable, physical process that makes a good source of entropy. They also have an attractive visual appeal that fits the concept [Joshua] had in mind. Unlike random number generators that kick off by measuring radiation or some other imperceptible thing, it’s possible — at least in a sense — to see this one working.
The small variations in the three neon lamps are measured optically by three TEPT4400 ambient light sensors (isolated from the neon lamps themselves) and turned into analog signals. A Raspberry Pi Pico W reads these signals, then uses them in a process that culminates in SHA-256 64-bit values that can be used as random seeds.
There’s also a web dashboard that shows everything live, furthering the “watch it work” concept [Joshua] is aiming for. The video below shows the project in action if you want to see how the sausage gets made.
Earlier we mentioned how random number generators are popular projects among hackers, and here are a few selected ones. Don’t miss the stylish glow and slick enclosure of this Nixie tube RNG, or the lava lamp RNG which is in fact not a gimmick. And while it is commonly understood that meaningful randomness must come from outside a digital chip, uninitialized internal volatile RAM — if accessed correctly — can be a remarkably good source of entropy.
Continue reading “This Random Number Generator Does It With Neon”