When it comes to cryptocurrency security, what’s the best way to secure the private key? Obviously, the correct answer is to write it on a sticky note and put it on the bezel of your monitor; nobody’ll ever think of looking there. But, if you’re slightly more paranoid, and you have access to a Falcon 9, you might just choose to send it to the Moon. That’s what is supposed to happen in a few months’ time, as private firm Lunar Outpost’s MAPP, or Mobile Autonomous Prospecting Platform, heads to the Moon. The goal is to etch the private key of a wallet, cheekily named “Nakamoto_1,” on the rover and fund it with 62 Bitcoins, worth about $1.5 million now. The wallet will be funded by an NFT sale of space-themed electronic art, because apparently the project didn’t have enough Web3.0 buzzwords yet. So whoever visits the lunar rover first gets to claim the contents of the wallet, whatever they happen to be worth at the time. Of course, it doesn’t have to be a human who visits.
Hackaday Columns4715 Articles
This excellent content from the Hackaday writing crew highlights recurring topics and popular series like Linux-Fu, 3D-Printering, Hackaday Links, This Week in Security, Inputs of Interest, Profiles in Science, Retrotechtacular, Ask Hackaday, Teardowns, Reviews, and many more.
Design For People
We all make things. Sometimes we make things for ourselves, sometimes for the broader hacker community, and sometimes we make things for normal folks. It’s this last category where it gets tricky, and critical. I was reminded of all of this watching Chris Combs’ excellent Supercon 2022 talk on how to make it as an artist.
“But I’m not making art!” I hear you say? About half of Chris’ talk is about how he makes his tech art worry-free for galleries to install, and that essentially means making it normie-proof – making sure it runs as soon as the power is turned on, day in, day out, without hacker intervention, because venues hate having you on site to debug. As Tom joked in the podcast, it’s a little bit like designing for space: it’s a strange environment, you can’t send out repair teams, and it has to have failsafes that make sure it works.
What is striking about the talk is that there is a common core of practices that make our hardware projects more reliable, whatever their destination. Things like having a watchdog that’ll reboot if it goes wrong, designing for modularity whenever possible, building in hanging or mounting options if that’s relevant, and writing up at least a simple, single-page info sheet with everything that you need to know to keep it running. Of course with art, aesthetics matters more than usual. Or does it?
So suppose you’re making a thing for a normal person, that must run without your babysitting. What is the common core of precautionary design steps you take?
Hackaday Podcast 213: Not Your Grandfather’s Grandfather Clock, The Engineering Behind Art, Hydrogen Powered Flight
Join Hackaday Editors Elliot Williams and Tom Nardi as they review some of their favorite hacks and projects of the past week. The episode starts with a discussion about the recently announced Artemis II crew, and how their mission compares to the Apollo program of the 1960s and 70s.
From there, the pair theorize as to why Amazon’s family of Echo devices have managed to evade eager hardware hackers, take a look at a very impressive SMD soldering jig created with some fascinating OpenSCAD code, marvel at the intersection of art and electronic design, and wonder aloud where all the cheap motorized satellite dishes are hiding. Stick around for some questionable PCB design ideas, a Raspberry Pi expansion that can read your mind, and the first flight of a (semi) hydrogen-powered aircraft.
Check out the links below if you want to follow along, and as always, tell us what you think about this episode in the comments!
This Week In Security: Cookie Monster, CyberGhost, NEXX, And Dead Angles
“Operation Cookie Monster” ranks as one of the best code names in recent memory. And it’s apropo, given what exactly went down. Genesis Market was one of those marketplaces where criminals could buy and sell stolen credentials. This one was a bit extra special.
Websites and services are getting better about detecting logins from unexpected computers. Your Google account suddenly logs in from a new computer, and a two-factor authentication challenge launches. Why? Your browser is missing a cookie indicating you’ve logged in before. But there’s more. Providers have started rolling out smart analytics that check for IP address changes and browser fingerprints. Your mix of time zone, user string, installed fonts, and selected language make a pretty unique identifier. So sites like Genesis offer Impersonation-as-a-Service (IMPaaS), which is session hijacking for the modern age.
A victim computer gets owned, and credentials are collected. But so are cookies and a browser fingerprint. Then a criminal buyer logs in, and runs a virtual browser with all that collected data. Run through a proxy to get a IP that is geolocated close enough to the victim, and Mr. Bad Guy has a cloned machine with all accounts intact.
And now back to Operation Cookie Monster, a multi-organization takedown of Genesis. It’s apparently a partial takedown, as the latest word is that the site is still online on the Tor network. But the conventional domains are down, and something like eight million credentials have been captured and added to the Have I Been Pwned database.
Another researcher team, Sector 7, has been working the case with Dutch authorities, and has some interesting details. The vector they cover was a fake activation crack for an antivirus product. Ironic. There are several extensions that get installed on the victim computer, and one of the most pernicious is disguised as Google Drive. This extension looks for a Command and Control server, using Bitcoin as DNS. A hardcoded Bitcoin address is polled for its latest transaction, and the receiving address is actually an encoded domain name, you-rabbit[.]com as of the latest check.
This extension will look for and rewrite emails that might be warning the victim about compromise. Get an email warning about a cryptocurrency withdrawal? It modifies it in the browser to be a sign-in warning. It also allows Genesis customers to proxy connections through the victim’s browser, bypassing IP address security measures. Continue reading “This Week In Security: Cookie Monster, CyberGhost, NEXX, And Dead Angles”
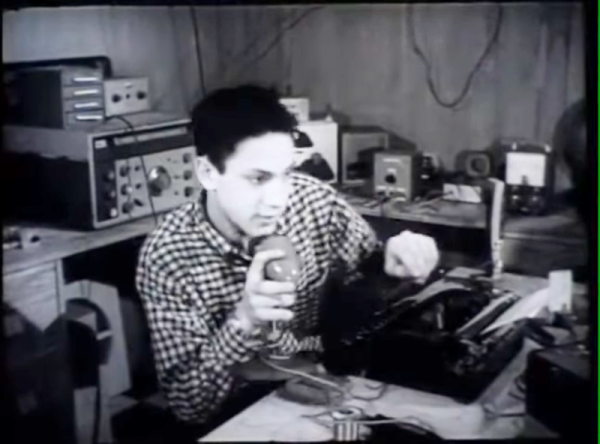
Retrotechtacular: Voice Controlled Typewriter Science Project In 1958
Hackaday readers might know [Victor Scheinman] as the pioneer who built some of the first practical robot arms. But what was a kid like that doing in high school? Thanks to a film about the 1958 New York City Science Fair, we know he was building a voice-activated typewriter. Don’t believe it? Watch it yourself below, thanks to [David Hoffman].
Ok, we know. Voice typing is no big deal today, and, frankly, [Victor’s] attempt isn’t going to amaze anyone today. But think about it. It was 1958! All those boat anchor ham radios behind him aren’t antiques. That’s what radios looked like in 1958. Plus, the kid is 16 years old. We’d say he did pretty darn good!
Continue reading “Retrotechtacular: Voice Controlled Typewriter Science Project In 1958”
Retrotechtacular: Solder Like Its 1944!
When we first saw this 1944 US Office of Education film about hand soldering, we figured it might still have some good information. Well, perhaps it does, but the 1944 soldering was with a giant iron, and the work looked more like metal bricks than anything we’ve soldered lately. Of course, the physics is all the same, but some of the terminology, like “sweating in” isn’t anything we’ve heard before, although we have heard of sweat soldering.
They do show some electronic soldering on components, including some interesting-looking coils. But the irons look more like a bad science fiction movie’s idea of a lightsaber. The solder is equally huge, of course.
Supercon 2022: Chris Combs Reveals His Art-World Compatibility Layer
[Chris Combs] is a full time artist who loves using technology to create unique art projects and has been building blinky artwork since about a decade now. In his 2022 Supercon talk “Art-World Compatibility Layer: How to Hang and Sell Your Blinky Goodness as Art” (Slides, PDF), [Chris] takes us behind the scenes and shows us how to turn our blinky doodads in to coveted art works. There is a big difference between a project that just works, and a work of art, and it’s the attention to small details that differentiates the two.
Just like the field of engineering and technology, the art world has its own jargon and requires knowledge of essential skills that make it intimidating to newcomers. It’s not very easy to define what makes an artwork “art” or even “Art”, and sometimes it’s difficult to distinguish if you are looking at a child’s scrawls or a master’s brushstrokes. But there are a few distinguishing requirements that a piece of artwork, particularly one revolving around the use of technology, must meet.
Continue reading “Supercon 2022: Chris Combs Reveals His Art-World Compatibility Layer”