Twitter just had their biggest security breach in years. Mike warned us about it on Wednesday, but it’s worth revisiting a few of the details. The story is still developing, but it appears that malicious actors used social engineering to access an internal Twitter dashboard. This dashboard, among other interesting things, allows directly changing the email address associated with an account. Once the address is changed to the attacker’s, it’s simple to do a password reset and gain access.
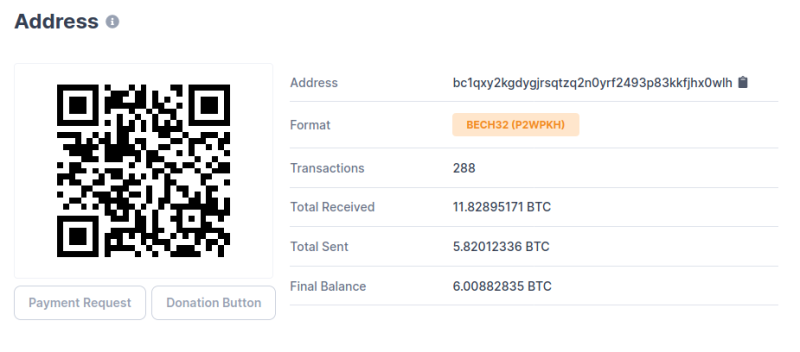
The bitcoin address used in the crypto scam ended up receiving nearly $120,000 USD worth of bitcoin, all of which has been shuffled off into different accounts. It’s an old and simple scam, but was apparently rather believable because the messages were posted by verified Twitter accounts.
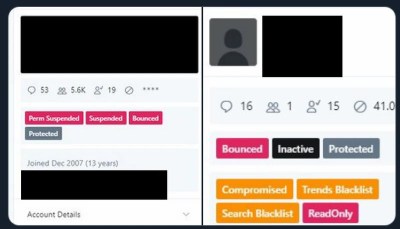
A series of screenshots have been posted, claiming to be the internal Twitter dashboard used in the attack. More than a few eyebrows have been raised, as a result of that dashboard. First off, the fact that Twitter employees can directly change an account’s email address is asking for trouble. Even more interesting are the tags that can be added to an account. “Trends Blacklist” and “Search Blacklist” do call to mind the rumors of shadow-banning, but at this point it’s impossible to know the details. Motherboard is reporting that Twitter is removing that screenshot across the board when it’s posted, and even suspending accounts that post it. Of course, they’d do that if it were faked as well, so who knows? Continue reading “This Week In Security: Twitter, Windows DNS, SAP RECON”