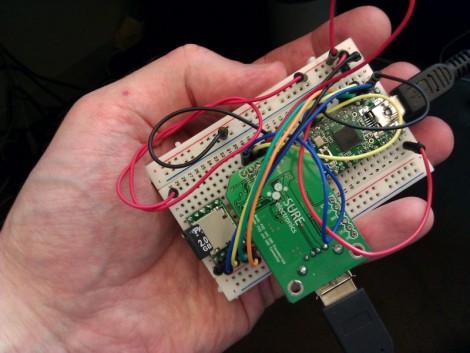
[Irongeek] is up to his old tricks once again with this new key logger prototype. It’s in the early stages, as attested by the breadboard built circuit, but [Adrian] still gives us a demo video after the break showing where he’s at right now. It comes in two flavors, the USB pass through seen above, or another that still connects to the computer via USB but functions with a PS/2 keyboard.
Aside from the obvious issue of a key logger stealing everything you type, there’s some prank value in this device too. The Teensy has more than enough processing power to watch what you typing and make changes as it goes. He shows off blatant rewrites, like changing “has” to “haz” or “you” to “U”. We think it would be better to change things like “they’re” to “their” or “it’s” to “its”. These would be very difficult to see happening and if you added randomness to how often the replacements occur, your victim would sooner come to the conclusion that they’re going crazy than that they’re the target of a little hazing. In fact, that’s probably the reason for our own grammar errors though the years; blast!
Continue reading “USB And PS/2 Key Loggers And Mess With Your Grammar”