Let’s face it – gamers have a reputation for being pretty lazy. In the most recent episode of his web series, [Ben Heck] takes on the stereotypical gamer role and cranks the laziness factor to 11, lamenting the fact that he needs to get up off the couch to swap discs in his Xbox 360 console. Never allowing laziness get in the way of his hacking, he springs into action, hauling off to his shop in order to construct an Xbox DVD changer system.
He grabbed a pair of CD changers and popped them open to see how they operated. After choosing the best candidate based on its CD loading method, he got to work disassembling the changer. The old CD player and its guts were removed, which he replaced with DVD drive components ripped from his Xbox. Quite a bit of trimming and tweaking was required to swap out the components, but it seems that [Ben] got things working just fine.
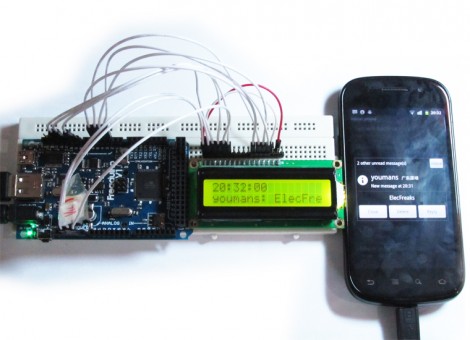
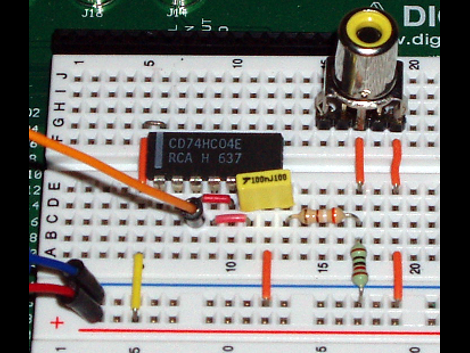
With the mechanical portion of the project out of the way, he dug into the electronics. The CD changer had no way of knowing how to interface with the Xbox and vice versa, so [Ben] had to devise a way for the two devices to communicate. He used an Arduino Uno to control the systems, triggering the CD carousel only when the Xbox thought it had its drive slot opened.
While the system looks a bit unpolished, and the controller quite bulky, we love this thing! No matter if you are lazy or not, jamming these two devices together is exactly what hacking is all about.