Two weeks ago, it was holographic cops. This week, it’s humanoid robot doctors. Or is it? We’re pretty sure it’s not, as MediBot, supposedly a $10,000 medical robot from Tesla, appears to be completely made up. Aside from the one story we came across, we can’t find any other references to it, which we think would make quite a splash in the media if it were legit. The article also has a notable lack of links and no quotes at all, even the kind that reporters obviously pull from press releases to make it seem like they actually interviewed someone.
blockchain25 Articles
Bitcoin Mining ASICs Repurposed To Keep NTP Server On Track
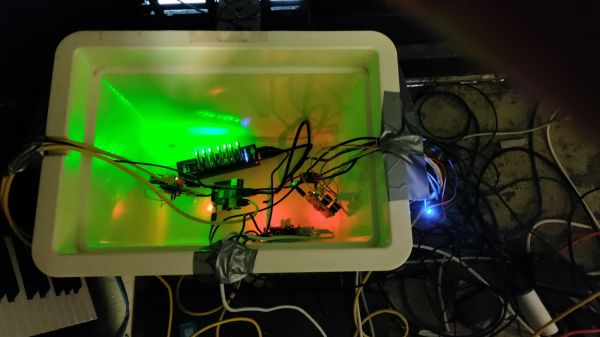
They say time is money, but if that’s true, money must also be time. It’s all figurative, of course, but in the case of this NTP server heater powered by Bitcoin mining dongles, money actually does become time.
This is an example of the lengths to which Network Time Protocol aficionados will go in search of slightly better performance from their NTP servers. [Folkert van Heusden], having heard that thermal stability keeps NTP servers happy, used a picnic cooler as an environmental chamber for his Pi- and GPS-based NTP rig. Heat is added to the chamber thanks to seven Block Erupter ASIC miner dongles, which are turned on by a Python script when a microcontroller sends an MQTT message that the temperature has dropped below the setpoint.
Each dongle produces about 2.5 Watts of heat when it’s working, making them pretty effective heaters. Alas, heat is all they produce at the moment — [Folkert] just has them working on the same hash over and over. He does say that he has plans to let the miners do useful work at some point, not so much for profit but to at least help out the network a bit.
This seems like a bit of a long way around to solve this problem, but since the mining dongles are basically obsolete now — we talked about them way back in 2013 — it has a nice hacky feeling to it that we appreciate.
This Week In Security: Through The Mouse Hole, Zoom RCE, And Defeating Defender
Windows security problems due to insecure drivers is nothing new, but this one is kinda special. Plug in a Razer mouse, tell the install dialog you want to install to a non-standard location, and then shift+right click the Explorer window. Choose a powershell, and boom, you now have a SYSTEM shell. It’s not as impressive as an RCE, and it requires hands-on the machine, but it’s beautiful due to the simplicity of it.
The problem is a compound one. First, Windows 10 and 11 automatically downloads and starts the install of Razer Synapse when a Razer device is plugged in. Note it’s not just Razer, any branded app that auto installs like this is possibly vulnerable in the same way. The installation process runs as system, and because it was started automatically, there is no admin account required. The second half of the issue is that the installer itself doesn’t take any precautions to prevent a user from spawning additional processes. There isn’t an obvious way to prevent the launch of Powershell from within the FolderPicker class, so an installer running as SYSTEM would have to go out of its way to drop privileges, to make this a safe process. The real solution is for Microsoft to say no to GUI installers bundled with WHQL signed drivers.
Continue reading “This Week In Security: Through The Mouse Hole, Zoom RCE, And Defeating Defender”
NFTs Are The Hope For A New Tomorrow!
Here at Hackaday, we’re always working as hard as we can to bring you the latest and most exciting technologies, and like so many people we’ve become convinced that the possibilities offered by the rise of the Blockchain present unrivaled opportunities for humanity to reinvent itself unfettered by the stifling regulations of a dying system. This is why today we’ve decided to join in with the digital cognoscenti and celebrities embracing Non-Fungible Tokens, or NFTs, as a new promise of non-corporeal digital investment cryptoasset that’s taking the world by storm.
Crypto Non-Fungible Investment Gains!

An NFT is a digital token representing something in the real world, and coupled to a unique ID held in a secure entry in the Blockchain. It’s non-fungible, which means that it’s unique and not interchangeable in the manner of a traditional old-style cryptoasset such as Bitcoin. As it allows a real-world object to be tokenised in digital form it represents a way to own something that provides an irrefutable connection to it as as a digital cryptoasset.
It’s a complex system that’s maybe too difficult to explain fully in a single article, but think of an NFT as a way to invest in a cryptoasset in digital form with its uniqueness guaranteed by Blockchain security, without having the inconvenience of physically owning it. Instead your NFT is safely held on a server on the Internet, and can’t be physically stolen as it would from a bank vault because it has the Blockchain cryptosecurity baked in.
Non Fungible Blockchain Cryptoassets!

NFTs have so far found a space in the creative markets, where they have provided a revolutionary opportunity for artists to expand their sales in the digital realm by selling NFTs of their work. A struggling artist can now access buyers all over the world, who can in turn now invest with confidence in creative talent to which they would never otherwise be exposed. It’s a win-win situation in which both cryptoinvestor and artist benefit from The Power of the Blockchain.
Hackaday is excited to offer a once-in-a-lifetime chance to acquire a Blockchain-cryptosecured NFT representing one of our own articles; our first ever NFT is the only officially sanctioned digital copy of a Hackaday article presenting a novel method of handling toilet paper shortages. The original article will continue to exist on Hackaday.com with all rights reserved, but we will not make any other NFTs of it. We may also decide to update the original article to let everyone know you are the lucky owner of the only digital copy of this piece of greatness. That’s right, this NFT will let you prove you own a screenshot!
Having today sold you on the incredible cryptoinvestment opportunity offered by NFTs, we’ll be back on another date with a more sober and in-depth technical examination of the technology behind them. Meanwhile should our brief foray into NFTs garner any interest (and we really hope it does not), we will donate proceeds to the excellent Girls Who Code, a truly solid investment with a tangible bright future.
Thanks [Micah Scott] for some NFT consultancy during the making of this piece.
To Kill A Blockchain, Add Naughty Stuff To It?
Even if not all of us are blockchain savants, we mostly have a pretty good idea of how they function as a distributed database whose integrity is maintained by an unbroken chain of conputational hashes. For cyryptocurrencies a blockchain ledger stores transaction records, but there is no reason why the same ledger can not contain almost any other form of digital content. [Bruce Schneier] writes on the potential consequences of content that is illegal or censored being written to a blockchain, and about how it might eventually form a fatal weakness for popular cryptocurrencies.
It’s prompted by the news that some botnet operators have been spotted using the Bitcoin ledger to embed command and control messages to hide the address of their control server. There have already been cases of illegal pornography being placed within blockchain ledgers, as well as leaked government data.
[Schneier] uses these two content cases to pose the question as to whether this might prove to be a vulnerability for the whole system. If a government such as China objects to a block containing censored material or a notoriously litigious commercial entity such as Disney objects to a piece of copyrighted content, they could take steps to suppress copies of the blockchain that contain those blocks. Being forced by hostile governments or litigious corporations to in effect remove a block from the chain by returning to the previous block would fork the blockchain, and as multiple forks would inevitably be made in this way it would become a threat to the whole. It’s an interesting possible scenario, and one that should certainly be ready by anyone with an interest in blockchain technologies.
Only a few weeks ago we looked at another threat to blockchain technologies – that they might be legislated out of existence by environmental rules.
What Uses More Power Than Argentina But Doesn’t Dance The Tango?
There’s been a constant over the last few weeks’ news, thanks to Elon Musk we’re in another Bitcoin hype cycle. The cryptocurrency soared after the billionaire endorsed it, at one point coming close to $60k, before falling back to its current position at time of writing of around $47k. The usual tide of cryptocurrency enthusiasts high on their Kool-Aid hailed the dawn of their new tomorrow, while a fresh cesspool of cryptocurrency scam emails and social media posts lapped around the recesses of the Internet.
This Time It’s Different!
The worst phrase that anyone can normally say about a financial bubble is the dreaded phrase “This time it’s different“, but there is something different about this Bitcoin hype cycle. It’s usual to hear criticism of Bitcoin for its volatility or its sometime association with shady deals, but what’s different this time is that the primary criticism is of its environmental credentials. The Bitcoin network, we are told, uses more electricity than the Netherlands, more than Argentina, and in an age where global warming has started to exert an uncomfortable influence over our lives, we can’t afford such extravagance and the emissions associated with them.
Here at Hackaday we are more concerned with figures than arguments over the future of currency, so the angle we take away from it all lies with those power stats. How much energy does Argentina use, and is the claim about Bitcoin credible?
Continue reading “What Uses More Power Than Argentina But Doesn’t Dance The Tango?”
Bringing The Blockchain To Network Monitoring
If you need to make sure your computer isn’t being messed with, you’ll have a look at the log files. If something seems fishy, that’s grounds for further investigation. If you run a large network of computers, you’ll probably want to look over all of the logs, but you won’t want to run around to each computer individually. Setting up a central server to analyze the logs exposes an additional attack surface: the logs in transit. How do you make sure that the attackers aren’t also intercepting and sanitizing your log file reports?
The answer to this question, and nearly everything else, is blockchain! Or maybe it’s not, but in this short presentation from the 2019 Hackaday Superconference, Shanni Prutchi, Jeff Wood, and six other college students intend to find out. While Shanni “rolls her eyes” at much of blockchain technology along with the rest of us, you have to admit one thing: recursively hashing your log data to make sure they’re not tampered with doesn’t sound like such a bad idea. Continue reading “Bringing The Blockchain To Network Monitoring”