The most collectible items in the realm of vintage computers often weren’t the most popular of their era. Quite the opposite, in fact. Generally the more desireable systems were market failures when they first launched, and are now sought out because of a newly-appreciated quirk or simply because the fact that they weren’t widely accepted means there’s fewer of them. One of the retro computers falling into this category is the Apple III, which had fundamental hardware issues upon launch leading to a large recall and its overall commercial failure. [Ted] is trying to bring one of these devices back to life, though, by slowing its clock speed down to a crawl.
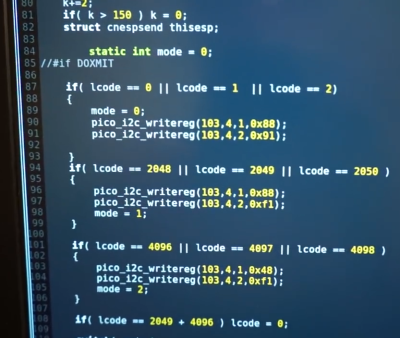
The CPU in these machines was a Synertek 6502 running at 1.8 MHz. With a machine that wouldn’t boot, though, [Ted] replaced it with his own MCL65+, a purpose-built accelerator card based on the 600 MHz Teensy 4.1 microcontroller in order to debug the motherboard. The first problem was found in a ROM chip which prevented the computer loading anything from memory, but his solution wouldn’t work at the system’s higher clock speeds. To solve that problem [Ted] disabled the higher clock speed in hardware, restricting the system to 1 MHz and allowing it to finally boot.
So far there haven’t been any issues running the computer at the slower speed, and it also helps keep the computer cooler and hopefully running longer as well, since the system won’t get as hot or unstable. This isn’t [Ted]’s first retrocomputing rodeo, either. His MCL chips have been featured in plenty of other computers like this Apple II which can run at a much faster rate than the original hardware thanks to the help of the modern microcontroller.