Among all the things you could find at MCH2022, there were a few CTFs (Capture The Flag exercises) – in particular, every badge contained an application that you could try and break into – only two teams have cracked this one! [dojoe] was part of one of them, and he has composed an extensive reverse-engineering story for us – complete with Ghidra disassembly of Xtensa code, remote code execution attempts, ROP gadget creation, and no detail left aside.
There was a catch: badges handed out to the participants didn’t contain the actual flag. You had to develop an exploit using your personal badge that only contained a placeholder flag, then go to the badge tent and apply your exploit over the network to one of the few badges with the real flag on them. The app in question turned out to be an echo server – sending back everything it received; notably, certain messages made it crash. One man’s crashes are another man’s exploit possibilities, and after a few hacking sessions, [dojoe]’s team got their well-deserved place on the scoreboard.
If you always thought that firmware reverse-engineering sounds cool, and you also happen to own a MCH2022 badge, you should try and follow the intricately documented steps of [dojoe]’s writeup. Even for people with little low-level programming experience, repeating this hack is realistic thanks to his extensive explanations, and you will leave with way more reverse-engineering experience than you had before.
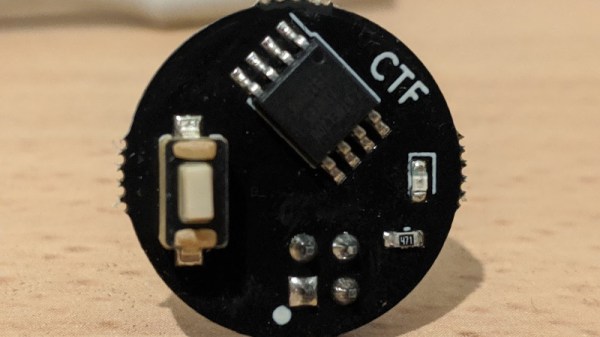
The MCH2022 badge is a featureful creation of intricate engineering, with the ESP32 portion only being part of the badge – we’re eager to hear about what you’ve accomplished or are about to accomplish given everything it has to offer!




 [Uri]’s project was
[Uri]’s project was