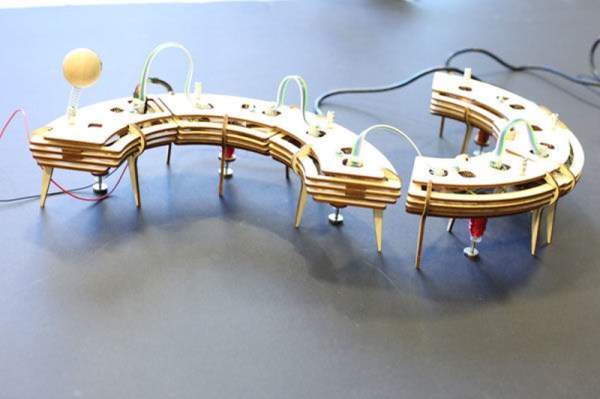
Electromechanical solenoids are pretty cool devices. Move some current through an electromagnet and you can push a load around or pull it. If you’re MIT student [Lining Yao], you can use them to dance. [Lining] built TapBot, a re-configurable set of tap-dancing robots that are both modular and modern. She even rolled her own solenoids.
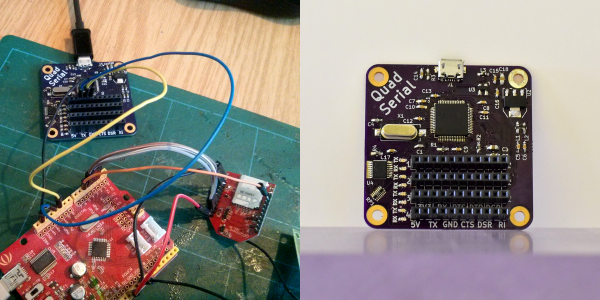
The one with the eye stalk is the bridge, and it’s connected to a computer over FTDI. The other nodes attach to the bridge and each other with small magnets that are designed to flip around freely to make the connections. These links are just physical, though. The nodes must also be connected with ribbon cables.
Each of the nodes is controlled by an ATtiny45 and has a MOSFET to drive the solenoid at 8-12 V. [Lining] snapped a small coin magnet to the end of each solenoid slug to provide a bigger surface area that acts like a tap shoe. TapBot can be programmed with one of several pre-built tap patterns, and these can be combined to make new sequences. The curtain goes up after the break.
There are other ways to make things dance, like muscle wire. Check out this whiteboard pen that uses nitinol to dance to Duke Nukem.
Continue reading “Modular Tap-Dancing Robot Can Shuffle Ball Change”