Homebrew wireless sensors are nothing new around these parts: grab an ESP8266, hang a BME280 from the I2C pins, and you’re just a few lines of code away from joining the Internet of Things on your own terms. Builds like this are so cheap and easy that they make an excellent first project for folks looking to get into the electronics game, but what if you’re looking for something a bit more bespoke?
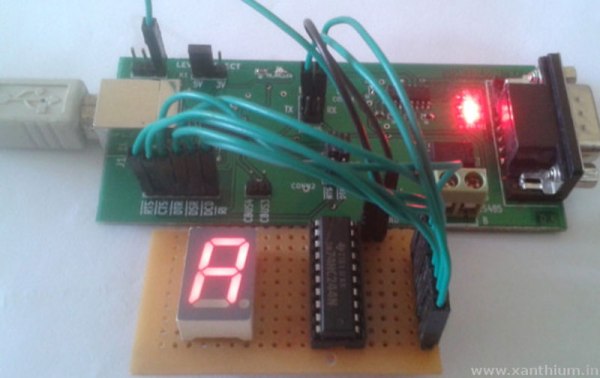
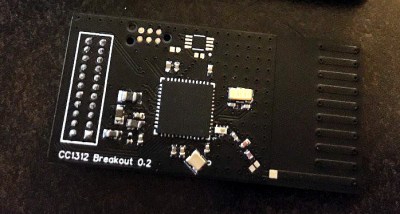
In that case, you could follow in the footsteps of [Discreet Mayor] and put together a custom modular architecture for long-range wireless sensors. The core of the system is a breakout board for the Texas Instruments SimpleLink CC1312 wireless MCU which features a simple 2×11 header connector. This allows the module to either be plugged into a larger board or have a small sensor PCB attached directly to it.
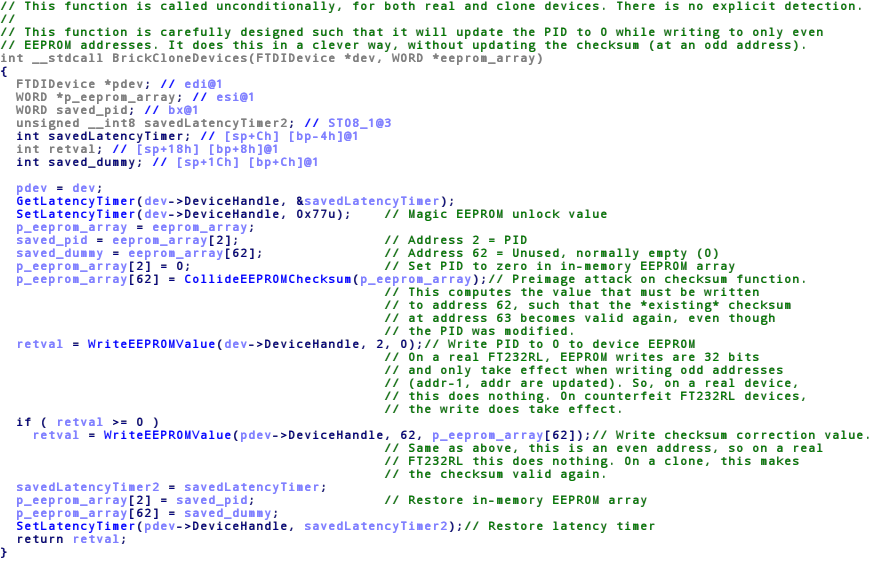
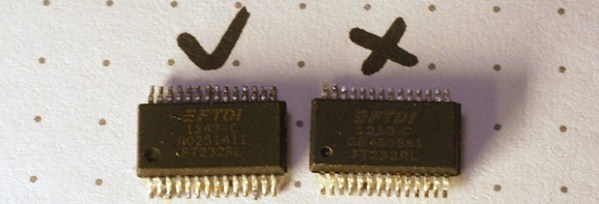
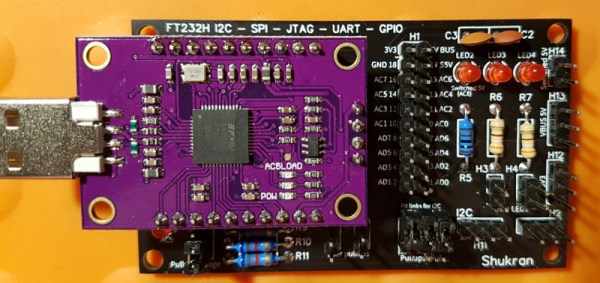
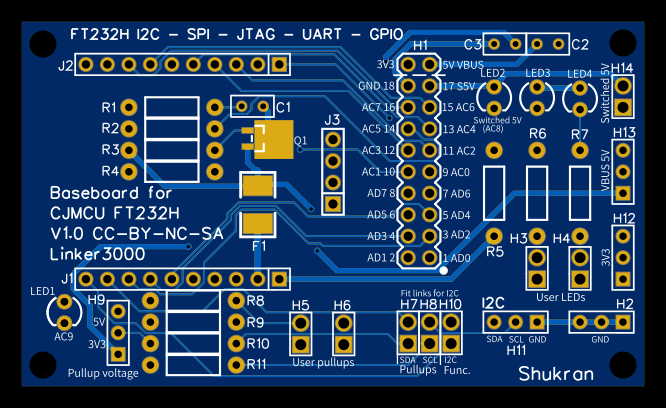
 Rather than using WiFi or requiring some existing radio infrastructure, the boards automatically create a private network using the IEEE 802.15.4 standard at a range of up to 600 meters. A dedicated receiver isn’t necessary, to pull data off the network, one of the CC1312 boards simply gets connected to a computer through a simple FT232 adapter.
Rather than using WiFi or requiring some existing radio infrastructure, the boards automatically create a private network using the IEEE 802.15.4 standard at a range of up to 600 meters. A dedicated receiver isn’t necessary, to pull data off the network, one of the CC1312 boards simply gets connected to a computer through a simple FT232 adapter.
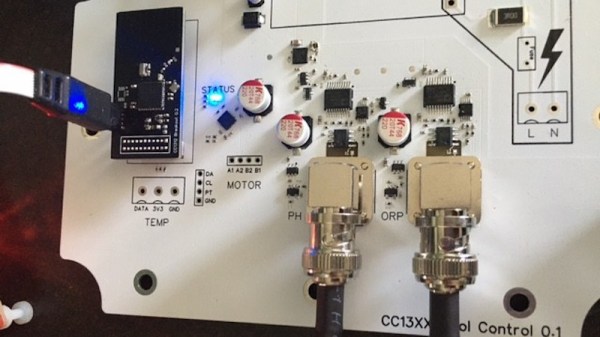
[Discreet Mayor] has already created a number of projects that use these custom radios for communication, from a pool monitoring system to a temperature sensor for the BBQ. That portable battery operated devices are able to use this common communications backbone just as well as mains powered static devices is a testament to the work that went into the firmware to make it as robust and efficient as possible.
Like the idea of long-range private networks, but less enthusiastic about having to come up with your own hardware? Not to worry. Over the summer, Espressif announced that they’re working on an ESP32 variant that includes support for IEEE 802.15.4. Just as soon as this chip shortage is over, we might even get to see the thing.

 The
The