If you are smart, you wouldn’t hand your house key over to a stranger for a few minutes, right? But every time you use your key to unlock your door, you are probably broadcasting everything an attacker needs to make their own copy. Turns out it’s all in the sound of the key going into the lock.
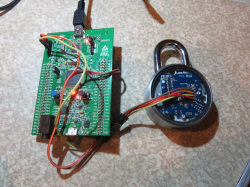
Researchers in Singapore reported that analyzing metallic clicks as the key slides past the pins gives them the data they need to 3D print a working key. The journal published research is behind a paywall, but there is a copy on co-author [Soundarya Ramesh’s] website which outlines the algorithm used to decode the clicks of key teeth on lock pins into usable data.
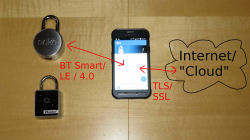
The attack didn’t require special hardware. The team used audio capture from common smartphones. While pushing your phone close to the lock while the victim inserts a key might be problematic, it isn’t hard to imagine a hacked phone or smart doorbell picking up the audio for an attacker. Long-range mikes or hidden bugs are also possible.
There are practical concerns, of course. Some keys have a plateau that causes some clicks to skip, so the algorithm has to deal with that. It sounds like the final result be a small number of key possibilities and not just converge on one single key, but even if you had to carry three or four keys with you to get in, it is still a very viable vulnerability.
The next step is to find a suitable defense. We’ve heard that softening the pins might reduce the click, but we wondered if it would be as well to put something in that deliberately makes loud clicks as you insert the key to mask the softer clicks of the pins.
While a sound recording is good, sometimes a picture is even better. Of course, if you want to go old school, you can 3D print your lockpicks.