We all know that you can play DOOM on nearly anything, but what about the lesser known work being done to let other species get in on the action? For ages now, our rodent friends haven’t been able to play the 1993 masterpiece, but [Viktor Tóth] and colleagues have been working hard to fix this unfortunate oversight.
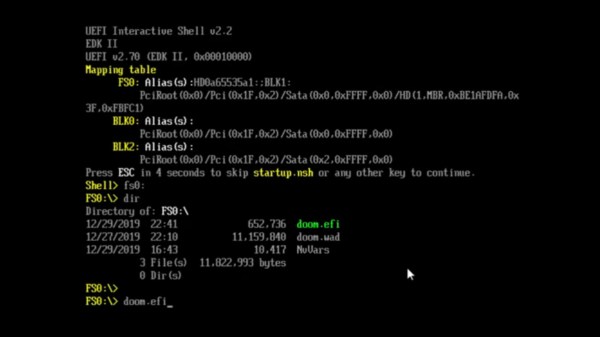
If you’ve got the feeling this isn’t the first time you’ve read about rats attempting to slay demons, it’s probably because [Victor] has been working on this mission for years now — with a previous attempt succeeding in allowing rats to navigate the DOOM landscape. Getting the rodents to actually play through the game properly has proved slightly more difficult, however.
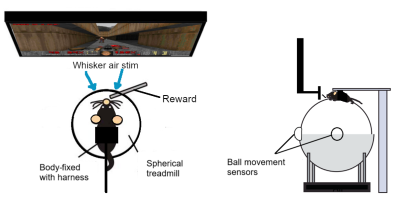
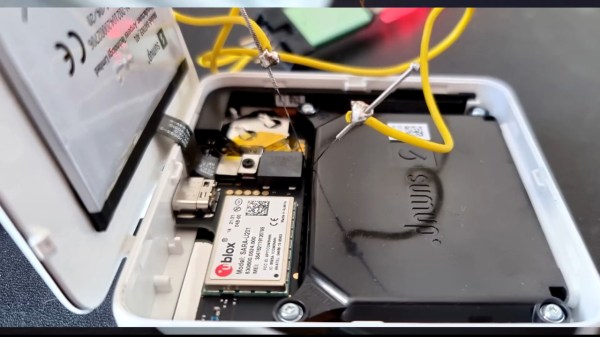
Improving on the previous attempt, V2 has the capability to allow rats to traverse through levels, be immersed in the virtual world with a panoramic screen, and take out enemies. Rewards are given to successful behaviors in the form of sugar water through a solenoid powered dispenser.
While this current system looks promising, the rats haven’t gotten too far though the game due to time constraints. But they’ve managed to travel through the levels and shoot, which is still pretty impressive for rodents.
DOOM has been an indicator of just how far we can take technology for decades. While this particular project has taken the meme into a slightly different direction, there are always surprises. You can even play DOOM in KiCad when you’re tired of using it to design PCBs.