A few days ago, Chinese researchers from technology giant Tencent released a paper outlining a firmware vulnerability in several types of fast charger power bricks (translated). The attack is known as BadPower, and it works by altering the default parameters in the firmware of fast chargers to deliver more power to devices than they can handle, which can cause them to overheat, melt, or catch fire.
The ancient and basic USB charging spec provides 0.5 A at 5 V, which is equal to 2.5 W. In theory, that’s all you’ll ever get from those types of chargers. But the newer generation of chargers are different. When you plug your phone into a fast charger, it negotiates a voltage and charging speed with your phone before passing it any power.
Fast chargers can push power at 20 V or more to speed up the charging process, depending on the charger and connected device. If the phone doesn’t do fast charging, it will default to the 5 V standard. Researchers claim the BadPower attack is capable of harming devices whether or not they include a fast charging feature. When a capable device is connected, the charger will still negotiate for 5V, but instead give 20V and wreak havoc.
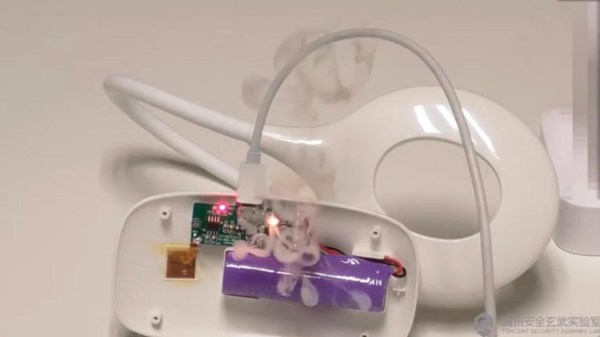
In the demo after the break, one of the team uses a malicious device disguised as a phone to push the BadPower firmware change to a fast charger that’s hooked up to a voltmeter. Before the attack, the charger gives 5V. After the attack, it gives 5V for a few seconds before jumping up near 20V. Then they connect the now-dirty charger to two identical illuminated magnifying glasses. In one the chip lets the smoke monster out rather violently, and the chips of the other emit sparks.
The researchers tested 35 of the 200+ fast charging bricks currently on the market and found that 18 of them were vulnerable to BadPower, including 11 that can be exploited through the charging port itself. They believe the issue is fixable with a firmware update.
What is not available is enough information to verify this research, or a list of brands/models that are vulnerable. Researchers say the findings were submitted to the China National Vulnerability Database (CNVD) on March 27th, so the absence of this information may be a product of manufacturers needing more time to patch the vulnerability.
What do you think? We say halfway decent chargers shouldn’t be open to firmware attacks from the devices they are charging. And any halfway decent phone should have built-in electrical protection, right?
Continue reading “BadPower Vulnerability In Fast Chargers Might Make Phones Halt And Catch Fire” →
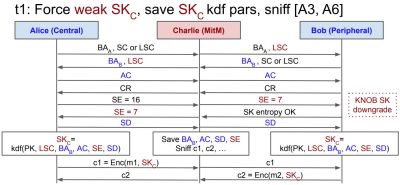 The name of this newly discovered vulnerability is BLUFFS (Bluetooth Forward and Future Secrecy), where forward and future secrecy are important terms that refer to the protection of secure sessions against compromise in the past (forward, FoS) and future (FuS). The CVE presentation notes that the Bluetooth specification does not cover either FuS or FoS. In total two new architectural vulnerabilities were discovered, both of which attack the security key.
The name of this newly discovered vulnerability is BLUFFS (Bluetooth Forward and Future Secrecy), where forward and future secrecy are important terms that refer to the protection of secure sessions against compromise in the past (forward, FoS) and future (FuS). The CVE presentation notes that the Bluetooth specification does not cover either FuS or FoS. In total two new architectural vulnerabilities were discovered, both of which attack the security key.