Sometimes it’s hard to read the tea leaves of what’s going on with high-profile space missions. Weighted down as they are with the need to be careful with taxpayer money and having so much national prestige on the line, space agencies are usually pretty cagey about what’s going on up there. But when project managers talk about needing a “miracle” to continue a project, you know things have gotten serious.
And so things now sit with Voyager 1, humanity’s most distant scientific outpost, currently careening away from Mother Earth at 17 kilometers every second and unable to transmit useful scientific or engineering data back to us across nearly a light-day of space. The problem with the 46-year-old spacecraft cropped up back in November, when Voyager started sending gibberish back to Earth. NASA publicly discussed the problem in December, initially blaming it on the telemetry modulation unit (TMU) that packages data from the remaining operable scientific instruments along with engineering data for transmission back to Earth. It appeared at the time that the TMU was not properly communicating with the flight data system (FDS), the main flight computer aboard the spacecraft.
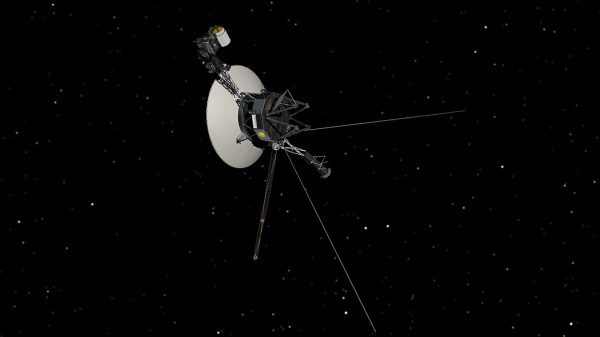
Since then, flight controllers have determined that the problem lies within the one remaining FDS on board (the backup FDS failed back in 1981), most likely thanks to a single bit of corrupted memory. The Deep Space Network is still receiving carrier signals from Voyager, meaning its 3.7-meter high-gain antenna is still pointing back at Earth, so that’s encouraging. But with the corrupt memory, they’ve got no engineering data from the spacecraft to confirm their hypothesis.
The team has tried rebooting the FDS, to no avail. They’re currently evaluating a plan to send commands to put the spacecraft into a flight mode last used during its planetary fly-bys, in the hope that will yield some clues about where the memory is corrupted, if indeed it is. But without a simulator to test the changes, and with most of the engineers who originally built the spacecraft long gone now, the team is treading very carefully.
Voyager 1 is long past warranty, of course, and with an unparalleled record of discovery, it doesn’t owe us anything at this point. But we’re not quite ready to see it slip into its long interstellar sleep, and we wish the team good luck while it works through the issue.