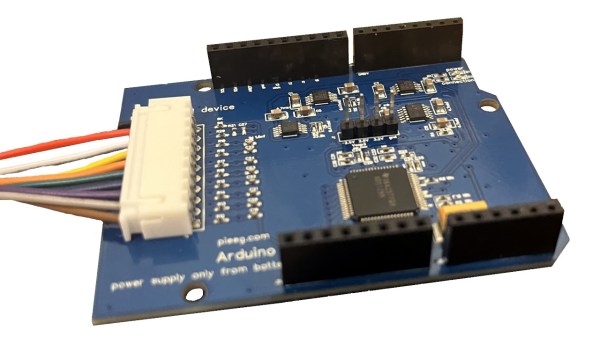
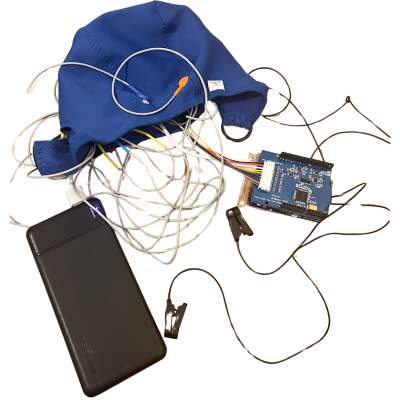
Detecting a cat with a raspberry pi and camera is one thing, but [Yoko Li]’s AI Raspberry Pi Cat Detection brings things entirely to another level by narrating your feline’s activities, nature documentary style.
The project is ostensibly aimed at tattling on the housecats by detecting forbidden behavior such as trespassing on the kitchen counter. But we daresay that’s overshadowed by the verbose image analysis, which describes the scene in its best David Attenborough impression.
This feline exemplifies both the beauty and the peaceful nature of its kind. No email will be sent as the cat is not on the kitchen counter.
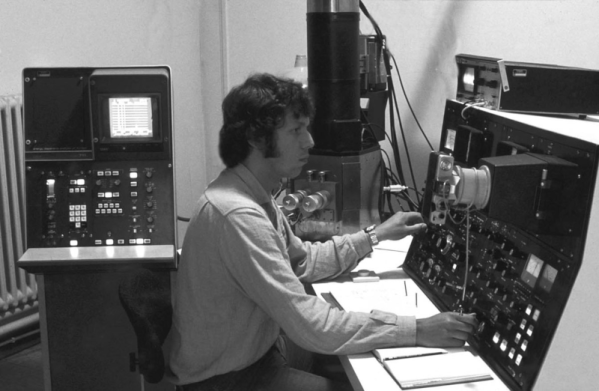
Hard to believe that just a few years ago this cat detector tool was the bee’s knees in cat detection technology. Things have certainly come a long way. Interested? The GitHub repository has everything needed to roll your own and we highly recommend watching it in action in the video, embedded below.
Continue reading “Raspberry Pi Narrates (And Tattles On) Your Cat, Nature Documentary Style”