These days, you can get fakes, bootlegs, and similar for just about anything. While a fake handbag isn’t such a big deal, in the case of a DIN-rail power supply, you’d better make sure that you got the real deal. Case in point, the fake ‘Mean Well’ DIN-rail PSU that [Big Clive] got his mitts on for a detailed analysis and teardown.
Even without taking a PSU apart there are often clear clues that you might be dealing with a fake, starting with the logo and the rest of the markings. Here it’s clear that the logo is designed to only appear to be the MW one at a quick glance, with the rest of the label being poorly copied English gibberish containing copious “unnecessary” double “quotes”.
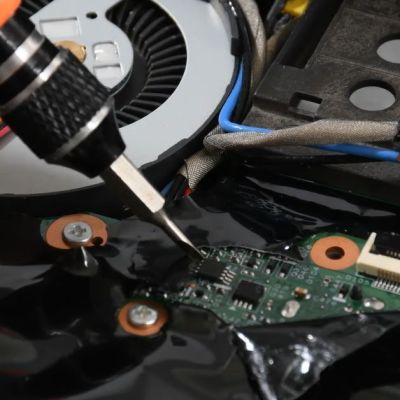
So what do you get for £3-5 in this +12VDC, 1.25A rated PSU? Shockingly, the insides are actually quite decent and probably close to the genuine MW, with basic noise filtering, proper isolation, and apparently a real class-Y safety capacitor. Similarly, the chosen DK124 control IC is more than capable of the task, with a good circuit for the adjustable voltage control.