It’s hard to believe, but the Raspberry Pi has now been around long enough that some of the earliest Pi projects could nearly be considered bonafide vintage hacks at this point. A perfect example are some of the DIY Raspberry Pi smartphone projects that sprung up a few years back. Few of them were terribly practical to begin with, but even if you ignore the performance issues and bulkiness, the bigger problem is they relied on software and cellular hardware that simply isn’t going to cut it today.
 Which was exactly the problem [Dylan Radcliffe] ran into when he wanted to create his own Pi smartphone. There was prior art to use as a guide, but the ones he found were limited to 2G cellular networks which no longer exist in his corner of the globe. He’s now taken on the quest to develop his own 3G-capable Pi smartphone, and his early results are looking very promising.
Which was exactly the problem [Dylan Radcliffe] ran into when he wanted to create his own Pi smartphone. There was prior art to use as a guide, but the ones he found were limited to 2G cellular networks which no longer exist in his corner of the globe. He’s now taken on the quest to develop his own 3G-capable Pi smartphone, and his early results are looking very promising.
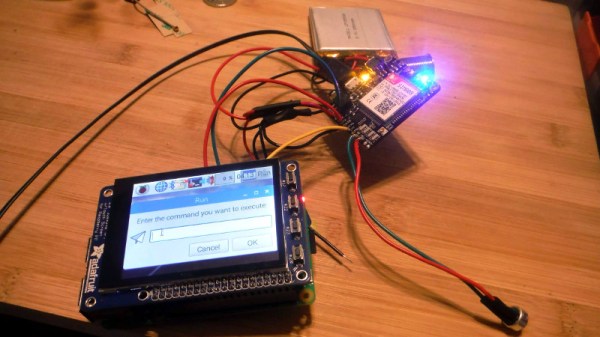
Inside the phone, which he calls the rCrumbl, [Dylan] has crammed a considerable amount of hardware. A Raspberry Pi 3B+ with attached Adafruit touchscreen LCD is the star of the show, but there’s also a Pi camera module, battery charging circuit, and Adafruit FONA 3G modem (which also provides GPS). Powering the device is a 2500 mAh 3.7V battery, which reportedly delivers a respectable 8 to 12 hour runtime.
 The case is 3D printed, and [Dylan] says it took a long time to nail down a design that would fit all of his hardware, keep things from shifting around, and still be reasonably slim. Obviously DIY phones like this are never going to be as slim as even the chunkiest of modern smartphones, but the rCrumbl looks fairly reasonable for a portable device. We especially like the row of physical buttons he’s included along the bottom of the screen, which should help with the device’s usability.
The case is 3D printed, and [Dylan] says it took a long time to nail down a design that would fit all of his hardware, keep things from shifting around, and still be reasonably slim. Obviously DIY phones like this are never going to be as slim as even the chunkiest of modern smartphones, but the rCrumbl looks fairly reasonable for a portable device. We especially like the row of physical buttons he’s included along the bottom of the screen, which should help with the device’s usability.
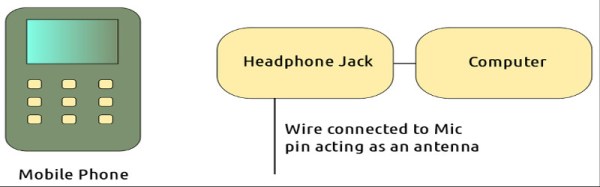
Speaking of usability, that’s where [Dylan] still has his work cut out for him. The existing software he’s found won’t work on 3G, so he’s going to have to come up with his own software stack to provide a proper phone interface. As it stands he’s made a call on the rCrumbl using command line tools, but while that might score you some extra geek points at the next hacker meetup, it’s not exactly going to fly for daily use. He mentions he would love to talk to any developers out there that would like to team up on the software side of the project.
We’ve covered one of the 2G Pi smartphones in the past, and of course the ZeroPhone is a very interesting project if you don’t mind the “dumb phone” interface. But if you’re looking for something that’s fairly close to commercial devices in terms of usability, you might just want to roll your own Android phone.