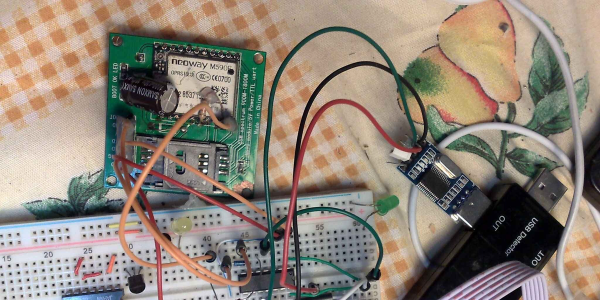
The Nokia 3310 has a reputation of being one of the most indestructible devices ever crafted by humanity. It’s also woefully out of date and only usable in a handful of countries that still maintain a GSM network. It might not be easy to bring it into the 5G era, but you can at least convert it to work with modern chargers, thanks to [Andrea].
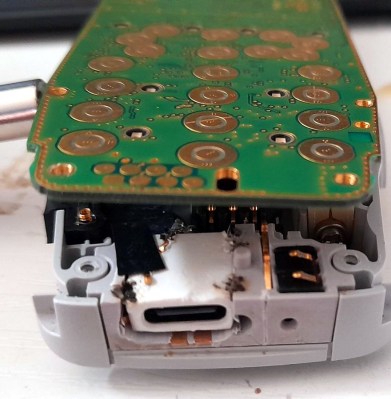
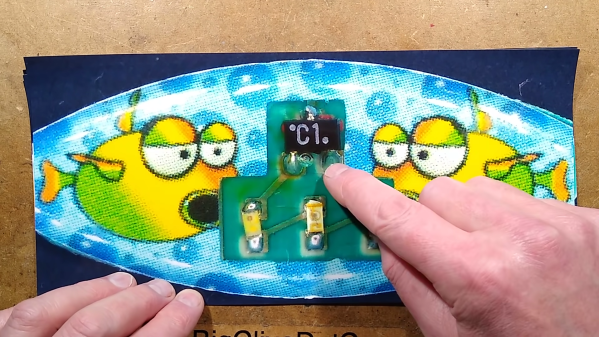
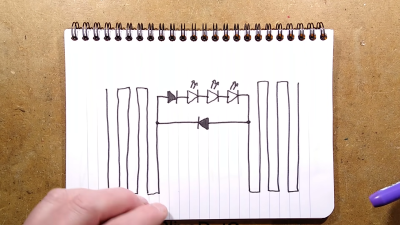
You might think this is a messy, complicated mod, but [Andrea] engineered it as a drop-in upgrade. He’s combined a USB-C port with a small plastic adapter that enables it to sit in place of the original phone’s charge port module. Contact between the port and the rest of the phone is via spring-loaded contacts. The only additional step necessary is popping out the mic from the original charge module and putting it in the new one. You need only a screw driver to disassemble the phone, swap out the parts, and put it all back together.
If you want to upgrade your own handset, [Andrea] is more than happy to provide the parts for a reasonable price of 25 euros. It’s almost worth it just for the laughs—head around to your friend’s house, ask to borrow a charger, and then plug in your USB-C 3310. You’ll blow some minds.
Once upon a time, it was big news that someone hacked a USB-C port into the iPhone. Video after the break.
Continue reading “The Nokia 3310 Finally Gets A USB-C Upgrade”