RF filters are really just a handful of strategically placed inductors and capacitors. Yes, you can make a 1 GHz filter out of through-hole components, but the leads on the parts turn into inductors at those frequencies, completely ruining the expected results in a design.
The solution to this is microstrip antennas, or carefully arranged tracks and pads on a PCB. Anyone can build one of these with Eagle or KiCad, but that means waiting for an order from a board house to verify your design. [VK2SEB] has a better idea for prototyping PCB filters: use copper tape on blank FR4 sheets.
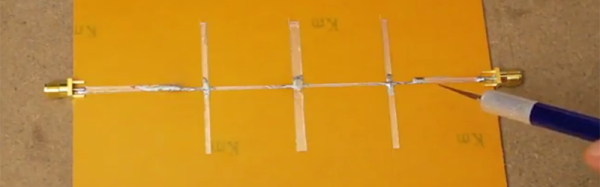
The first, and simplest, filter demonstrated is a simple bandstop filter. This is really just a piece of fiberglass with copper laminated to one side. Two RF connectors are soldered to the edges and a strip of copper tape strung between them. Somewhere around the middle of this copper tape, [VK2SEB] put another strip of copper tape in a ‘T’ configuration. This is the simplest bandstop filter you can make, and the beauty of this construction is that it can be tuned with a razor blade.
Of course, a filter can only be built with copper tape if you can design them, and for that [SEB] is turning to software. The Qucs project is a software tool for designing and simulating these microstrip filters, and after inputting the correct parameters, [SEB] got a nice diagram of what the filter should look like. A bit of taping, razor blading, and soldering and [SEB] had a working filter connected to a spectrum analyzer. Did it work? To a limited extent; the PCB material probably wasn’t right, and board houses are more accurate than a razor blade, but [SEB] did manage to create a 10 GHz filter out of fiberglass and copper tape.
You can check out the video for this experiment below.