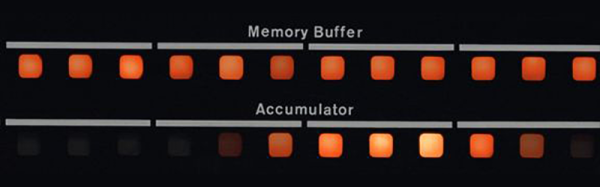
Years ago when the old mainframes made their way out of labs and into the waiting arms of storage closets and surplus stores, a lot got lost. The interesting bits – core memory boards and the like – were cool enough to be saved. Some iconic parts – blinkenlight panels – were stashed away by techs with a respect for our computing history.
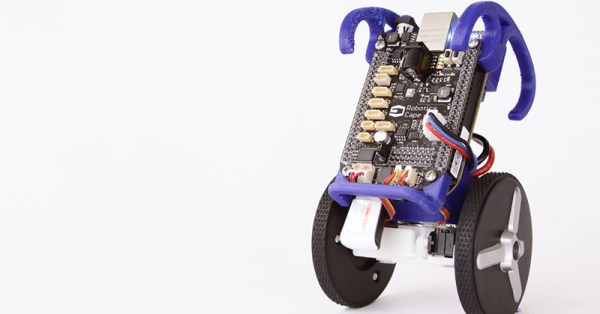
For the last few years, [Jörg] has been making these blinkenlight panels work again with his BlinkenBone project. His work turns a BeagleBone into a control box for old console computers, simulating the old CPUs and circuits, allowing them to work like they did thirty years ago, just without the hundreds of pounds of steel and kilowatts of power. Now, [Jörg] has turned to a much smaller and newer blinkenlight panel, the PiDP-8.
The PiDP-8 is a modern, miniaturized reproduction of the classic PDP 8/I, crafted by [Oscar Vermeulen]. We’ve seen [Oscar]’s PiDP a few times over the last year, including a talk [Oscar] gave at last year’s Hackaday Supercon. Having a simulated interface to a replica computer may seem ridiculous, but it’s a great test case for the interface should any older and rarer blnkenlight panels come out of the woodwork.