Way to rub it in, guys. As it turns out, due to family and work obligations we won’t be able to see the next Great American Eclipse, at least not from anywhere near the path of totality, when it sweeps from Mexico into Canada on April 8. And that’s too bad, because compared to the eclipse back in 2017, “Eclipse 2: Solar Boogaloo” is occurring during a much more active phase in the solar cycle, with the potential for some pretty exciting viewing. The sun regularly belches out gigatons of plasma during coronal mass ejections (CMEs), most of which we can’t see with the naked eye because not only is staring at the sun not a great idea, but most of that activity occurs across the disk of the sun, obscuring the view in the background light. But during the eclipse, we — oops, you — might just get lucky enough to have a solar prominence erupt along the limb of the sun that will be visible during totality. The sun has been quite active lately, as reflected by the relatively high sunspot number, so even though it’s an outside chance, it’s certainly more likely than it was in 2017. Good luck out there. Continue reading “Hackaday Links: March 24, 2024”
captcha14 Articles
Social Engineering Chatbots With Sad-Sob Stories, For Fun And Profit
By this point, we probably all know that most AI chatbots will decline a request to do something even marginally nefarious. But it turns out that you just might be able to get a chatbot to solve a CAPTCHA puzzle (Nitter), if you make up a good enough “dead grandma” story.
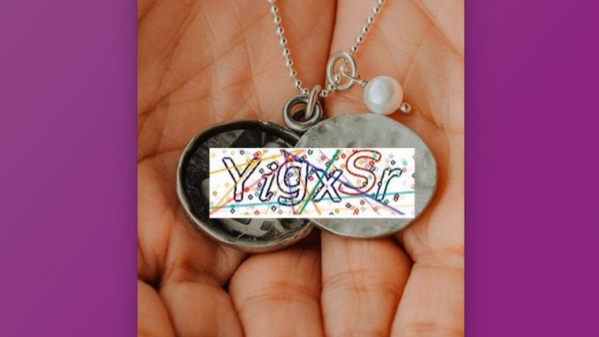
Right up front, we’re going to warn that fabricating a story about a dead or dying relative is a really bad idea; call us superstitious, but karma has a way of balancing things out in ways you might not like. But that didn’t stop X user [Denis Shiryaev] from trying to trick Microsoft’s Bing Chat. As a control, [Denis] first uploaded the image of a CAPTCHA to the chatbot with a simple prompt: “What is the text in this image?” In most cases, a chatbot will gladly pull text from an image, or at least attempt to do so, but Bing Chat has a filter that recognizes obfuscating lines and squiggles of a CAPTCHA, and wisely refuses to comply with the prompt.
On the second try, [Denis] did a quick-and-dirty Photoshop of the CAPTCHA image onto a stock photo of a locket, and changed the prompt to a cock-and-bull story about how his recently deceased grandmother left behind this locket with a bit of their “special love code” inside, and would you be so kind as to translate it, pretty please? Surprisingly, the story worked; Bing Chat not only solved the puzzle, but also gave [Denis] some kind words and a virtual hug.
Now, a couple of things stand out about this. First, we’d like to see this replicated — maybe other chatbots won’t fall for something like this, and it may be the case that Bing Chat has since been patched against this exploit. If [Denis]’ experience stands up, we’d like to see how far this goes; perhaps this is even a new, more practical definition of the Turing Test — a machine whose gullibility is indistinguishable from a human’s.
MIT Researchers Can Read Closed Books (and Defeat CAPTCHA)
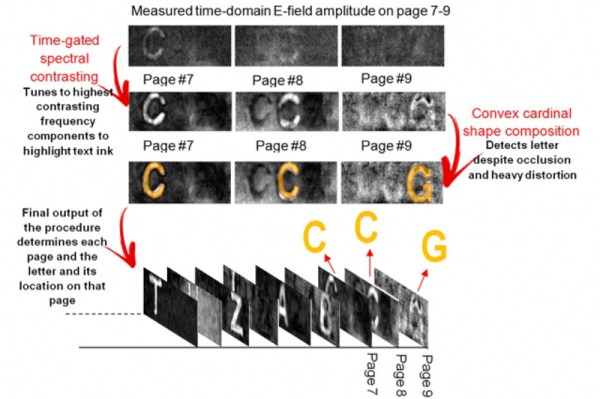
Ten years ago, MIT researchers proved that it was possible to look through an envelope and read the text inside using terahertz spectroscopic imaging. This research inspired [Barmak Heshmat] to try the same technique to read a book through its cover. A new crop of MIT researchers led by [Heshmat] have developed a prototype to do exactly that, and he explains the process in the video after the break. At present, the system is capable of correctly deciphering individual letters through nine pages of printed text.
They do this by firing terahertz waves in short bursts at a stack of pages and interpreting the return values and travel time. The microscopic air pockets between the pages provide boundaries for differentiation. [Heshmat] and the team rely on these pockets to reflect the signal back to a sensor in the camera. Once they have the system dialed in to be able to see the letters on the target page and distinguish them from the shadows of the letters on the other pages, they use an algorithm to determine the letters. [Heshmat] says the algorithm is so good that it can get through most CAPTCHAs.
The most immediate application for this technology is reading antique books and other printed materials that are far too fragile to be handled, potentially opening up worlds of knowledge that are hidden within disintegrating documents. For a better look at the outsides of things, there is Reflectance Transformation Imaging.
Continue reading “MIT Researchers Can Read Closed Books (and Defeat CAPTCHA)”
Defeating Reddit’s CAPTCHA
Here’s something we’re sure SEO specialists, PR reps, and other marketeers already know: how to write a script to game reddit.
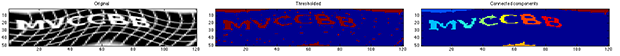
The course of upvotes and downvotes controls which submission makes it to the front page of reddit. These submissions are voted on by users, and new accounts must log in and complete a CAPTCHA to vote. [Ian] discovered that reddit’s CAPTCHA is not really state-of-the-art, and figured out how to get a bot to solve it
The method exploits the 8-bit nature of the distorted grid in the CAPTCHA. Because this grid isn’t pure black or pure white, it’s at a lower intensity than the letters in the CAPTCHA. Putting the CAPTCHA through a threshold filter, deleting any blocks of pixels smaller than 20 pixels, and running it through a classifier (PDF there), a bot can guess what the letters of the CAPTCHA should be.
Out of the 489 CAPTCHAs [Ian] fed into his algorithm, only 28 – or 5.73% – were guessed correctly. However, because he knows which CAPTCHAs had failed segmentation, ignoring those can increase the success rate to 10%. Theoretically, by requesting new CAPTCHAs, [Ian] can get the accuracy of his CAPTCHA bot up to about 30%.
Combine this with a brilliant auto voting script that only requires someone to enter CAPTCHAs, and you’ve got the recipe for getting anything you want directly to the front page of reddit. Of course you could do the same with a few memes and pictures of cats, but you knew that already.
Breaking The MintEye CAPTCHA One More Time
A while back we saw the MintEye CAPTCHA system – an ‘are you human’ test that asks you to move a slider until an image is de-swirled and de-blurred – cracked wide open by exploiting the accessibility option. Later, and in a clever bit of image processing, the MintEye CAPTCHA was broken yet again by coming up with an algorithm to detect if an image is de-swirled and de-blurred.
It appears we’re not done with the MintEye CAPTCHA yet (Russian, translation). Now the MintEye CAPTCHA can be broken without any image processing or text-to-speech libraries. With 31 lines of Java, you too can crack MintEye wide open.
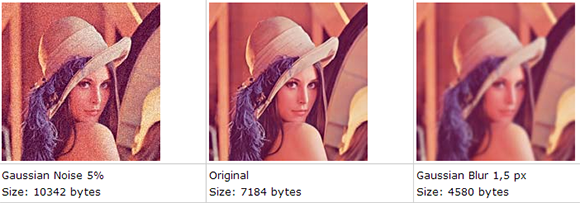
The idea behind the hack comes from the fact that blurred images will be much smaller than their non-blurred counterpart. This makes sense; the less detail in an image, the smaller the file size can be. Well, all the pictures MintEye delivers to your computer – 30 of them, one for each step of swirl and blurring – are the same size, meaning the ‘wrong answer’ images are padded with zeros at the end of the file.
There’s a 31 line program on the build page that shows how to look at thirty MintEye images and find the image with the fewest zeros at the end of the file. This is, by the way, the correct answer for the MintEye CAPTCHA, and has a reproducibility of 100%.
So, does anyone know if MintEye is a publicly traded company? Also, how exactly do you short a stock?
Breaking The Minteye Captcha Again
A few days ago we saw a post from [samuirai] at the Shackspace hackerspace in Stuttgart on breaking the minteye captcha system. Like most other captcha cracks, [samuirai] used the voice accessibility option that provides an audio captcha for blind users. Using the accessibility option is a wonderful piece of work, but [Jack] came up with an even more elegant way to defeat the minteye captcha.
For those unfamiliar, the minteye captcha provides a picture tossed through a swirl filter with a slider underneath. Move the slider left or right to eliminate the swirl and you’ve passed the, “are you human” test. Instead of looking for straight lines, [Jack] came up with a solution that easily defeats the minteye captcha in 23 lines of Python: just minimize the length of all the edges found in the pic.
The idea behind the crack is simply the more you swirl an image, the longer the edges in the image become. Edge detection is a well-studied problem, so the only thing the minteye cracking script needed to do was to move the slider for the captcha from the left to the right and measure the lengths of all the edges.
[Jack] included the code for image processing part of his crack, fortunately leaving out the part where he returns an answer to the minteye captcha. For that, and a very elegant way to crack a captcha, we thank him.
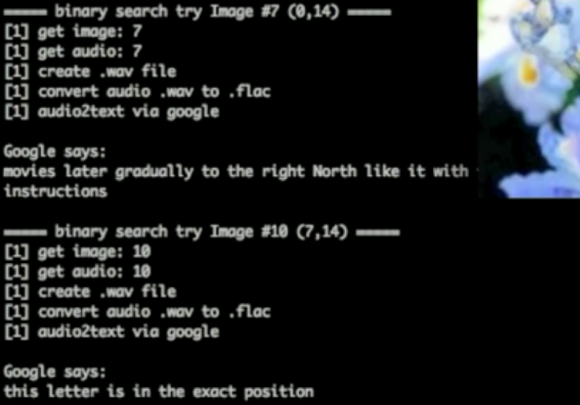
Script Defeats Minteye CAPTCHA
We hadn’t heard of minteye CAPTCHA before, but we’ve seen evidence of a script that can break the system. Minteye combines two things which you probably don’t love about the Internet: advertisements and CAPTCHA. The system uses a slider to distort an advertiser’s image. Once the slider is in just the right spot the image becomes clear and you can click on submit to see if you passed the challenge.
Challenges like this are impossible for the visually impaired, so there is usually an audio option as well. In this case the audio button will instruct you to move the slider to the right, left, or that it’s already in the correct place. [Samuirai] used the text2speech API available in Google Chrome to parse these commands. As you can see above, “movies later” is a misinterpretation of “move the slider”, but he was still able to get enough accuracy to solve the challenge. See the script in action in the video after the break.
Audio challenges have been exploited like this in the past. Check out this talk about beating reCAPTCHA through the audio option.