If there’s something weird in your Network Neighborhood, who you gonna call? If you want your WiFi troubles diagnosed in style, try calling [Travis Kaun] — he might just show up wearing the amazing Pwnton Pack. Built from a replica Proton Pack similar to those used in the 1984 classic Ghostbusters, it’s a portable wireless security diagnostics kit that should be able to pinpoint any weaknesses in your wireless network.
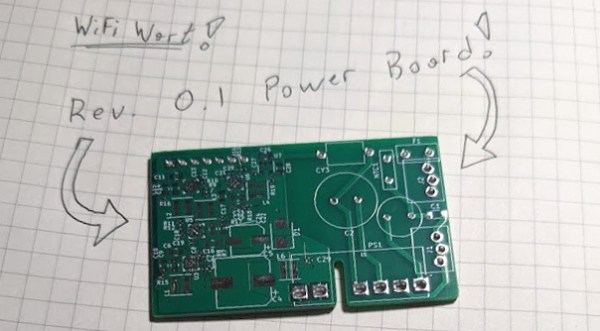
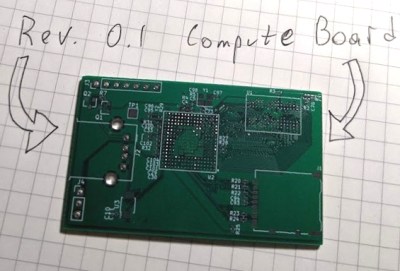
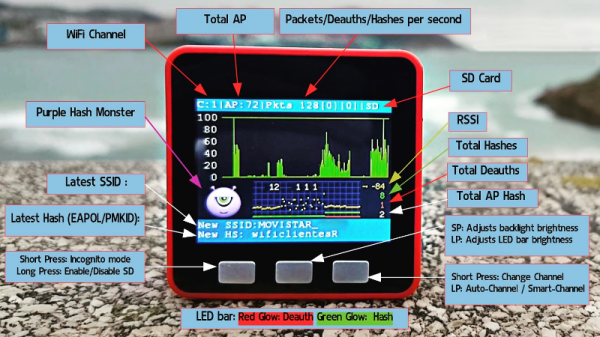
Inside, it’s got a Mark VII WiFi Pineapple, which is a portable device designed for security testing purposes, as well as a Raspberry Pi running Pwnagotchi: a deep learning-based WiFi sniffer that aims to capture those network packets that help maximize your chances of brute-forcing the WPA key. These two devices are connected to an array of antennas, including a cool rotating 5 GHz panel antenna to scan the surrounding area.
Naturally, the Pwnton Pack also includes a Neutrona Wand, which in this case contains a 2.4 GHz Yagi antenna hooked up to an ESP32 programmed to perform deauthentication attacks. An Arduino Nano drives an LED matrix that shows scrolling Pac-Man ghosts, while a dedicated sound board provides movie sound effects. The whole system is powered by three LiPo battery packs, and can even be remotely operated if desired.
Sadly, it doesn’t come with one of those ghost traps to suck up wayward WiFi networks, but the range of tools available should help to catch any kind of weird phantoms hiding in your system. We’ve spotted a few Proton Packs before, but never one with such advanced functionality. Security testing systems tend to be a bit less conspicuous, after all. Continue reading “Track Down Ghosts In Your WiFi With The Pwnton Pack”