It’s not uncommon for a radio enthusiast to have multiple antennas for the same radio, so as you might expect it’s also entirely usual to have a bunch of coaxial cables dangling down for fumbling around the back of the rig to swap over. If that describes your radio experience than you might be interested in the antenna switcher built by [g3gg0], which uses solid-state RF switches controlled by an ESP32 module.
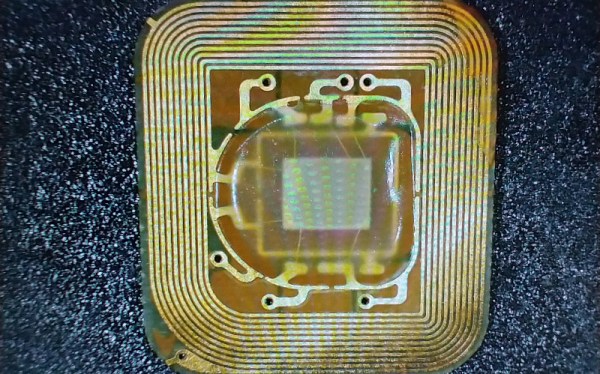
At its heart is the MXD8625C RF switch, a tiny device designed for cellular phone applications that delivers only a fraction of a dB insertion loss and somehow negates the need for any blocking capacitors. It’s controlled by a GPIO line, and he’s hooked up a brace of them to allow the distribution of three antennas to a couple of radios with the handy option of switching in a preamplifier if required. Of even more interest we note that the device is suitable for transmitter switching too, with a maximum 36.5 dBm throughput that we calculate to be about 4.5 W. This board is fairly obviously for receive use, but perhaps the chip is of interest to anyone considering a transceiver project. Meanwhile the software is a relatively simple web-based control linking on-screen controls to GPIOs.
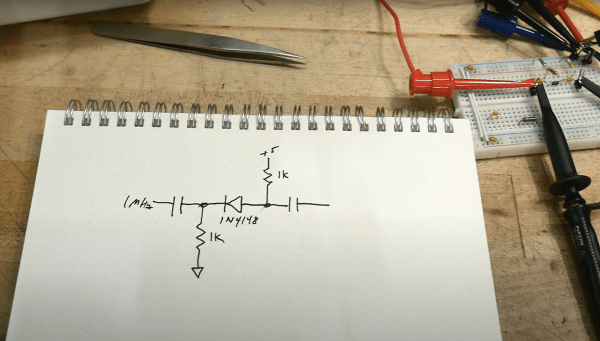
If you are interested in solid state RF switches, it’s always worth remembering that at lower frequencies they can be very simple indeed.