The camera lens on the iPhone is much like any other cameraphone lens in the fact that the lens has a fixed minimum and maximum focus length. If you want to get a little closer to your subject, you just might want to give [eastrain’s] macro camera mod a try.
According to [eastrain] both first and second generation iPhone cameras have a screw type focus ring that has been glued to infinity from the factory. This was probably set so that 99% of your photos were roughly in focus.
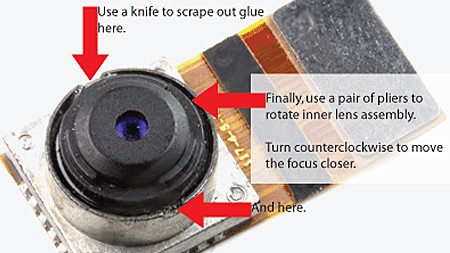
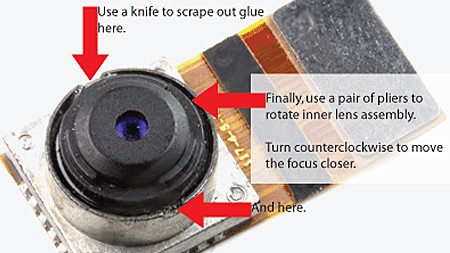
Gaining access to the camera lens requires the disassembly of your phone and will undoubtedly void any type of warranty you may have had. Once the lens is in view you will need to break the 2 glue points that hold the lens at its current position.
Using needle nose pliers you can then rotate the lens counter clockwise to increase the zoom or clockwise to decrease it. Enabling the built in camera app allows you to see in real time your changes. When you’re satisfied, just put everything back together. Of course the next step should be an externally mounted ring to allow manual zooming on the fly.