One of our favorite things about the rise of hobbyist development ecosystems such as the Arduino is that it’s now possible to make a MIDI controller out of almost anything, as long as you have the the shields and the dedication. We’re glad that [James Bruton] takes the occasional break from making robots to detour into instrument making, because his latest creation turns it up to 11.
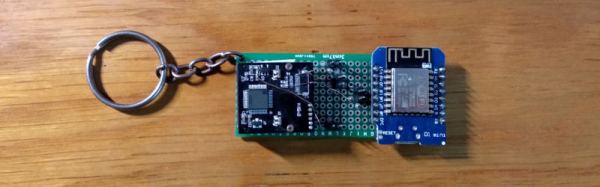
This awesome guitar uses a barcode scanner to play notes, and various arcade controls to manipulate those notes. The barcodes themselves scan as ASCII values, and their equivalent integers are sent to an external MIDI device. This futuristic axe is built on an Arduino Mega, with a USB shield for the barcode scanner, and a MIDI shield on top that [James] connects to various synths in the video after the break.
In between shooting barcodes, the right hand also controls octave shifting and changing MIDI channels with the joystick, and doing pitch-bends with the rotary encoder. The array of arcade buttons on the bottom neck let him switch between single player for monophonic synths, and multiplayer for polys. The other three buttons are press-and-scan programmable single-note sounders that assist in chord-making and noodling.
We particularly dig the construction, which is a combination of 20/20 and 3D printed boxes. [James] found some angled PVC to serve as fretboards for the four necks, and a nice backgrounds for bar codes.The only thing we would change is the native beep of the barcode scanner — either silence it forever or make it mutable, because it doesn’t jive with every note. It might be nice to get the gun to scan continuously so [James] doesn’t get trigger finger. Or better yet, build the scanner into a glove.
Want to do something more useful with that barcode scanner in your parts bin? Use it to manage your household inventory. But first, reacquaint yourself with the history of the humble barcode as presented by [Adam Fabio].
Continue reading “Barcode Guitar Plays More Than Beep-Bop” →