When facing a malware situation, the usual “guaranteed solution” is to reinstall your OS. The new developments in malware world will also require you to have a CH341 programmer handy. In an arguably inevitable development, [Kaspersky Labs] researchers have found an active piece of malware, out in the wild, that would persist itself by writing its bootstrap code into the BIOS chip. It doesn’t matter if you shred the HDD and replace it with a new one. In fact, so-called MoonBounce never really touches the disk at all, being careful to only store itself in RAM, oh, and the SPI flash that stores the BIOS code, of course.
MoonBounce is Microsoft-tailored, and able to hook into a chain of components starting from the UEFI’s DXE environment, through the Windows Loader, and finishing as a part of svchost.exe, a process we all know and love.
This approach doesn’t seem to be widespread – yet, but it’s not inconceivable that we’ll eventually encounter a ransomware strain using this to, ahem, earn a bit of extra cash on the side. What will happen then – BIOS reflashing service trucks by our curbsides? After all, your motherboard built-in BIOS flasher UI is built into the same BIOS image that gets compromised, and at best, could be disabled effortlessly – at worst, subverted and used for further sneaky persistence, fooling repairpeople into comfort, only to be presented with one more Monero address a week later.
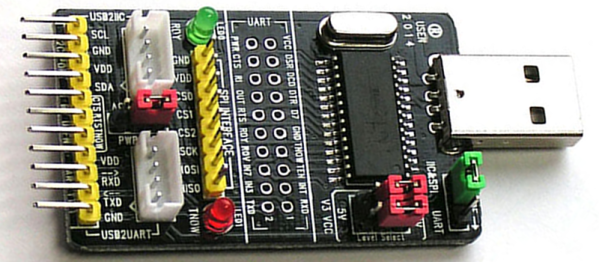
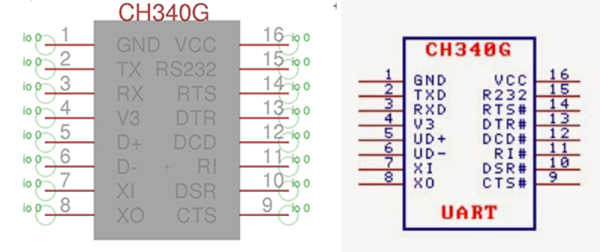
Will our hardware hacker skills suddenly go up in demand, with all the test clip fiddling and SOIC-8 desoldering being second nature to a good portion of us? Should we stock up on CH341 dongles? So many questions!
This week’s installment of “threat vectors that might soon become prevalent” is fun to speculate about! Want to read about other vectors we might not be paying enough attention to? Can’t go wrong with supply-chain attacks on our repositories! As for other auxiliary storage-based persistence methods – check out this HDD firmware-embedded proof-of-concept rootkit. Of course, we might not always need the newfangled ways to do things, the old ways still work pretty often – you might only need to disguise your malicious hardware as a cool laptop accessory to trick an average journalist, even in a hostile environment.
Continue reading “Is That The Moon Worming Its Way Into Your BIOS?”