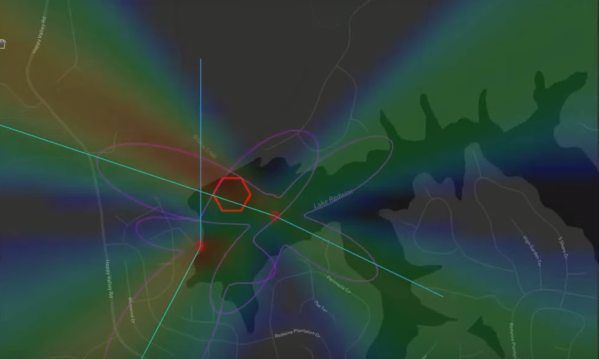
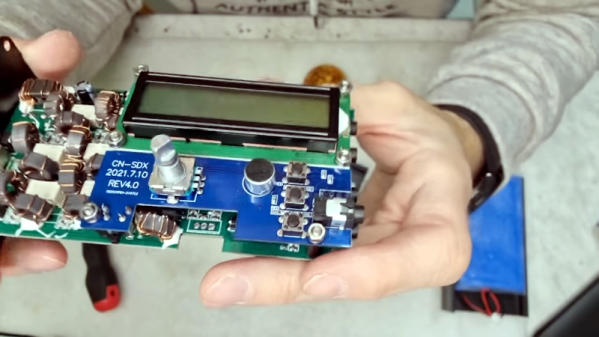
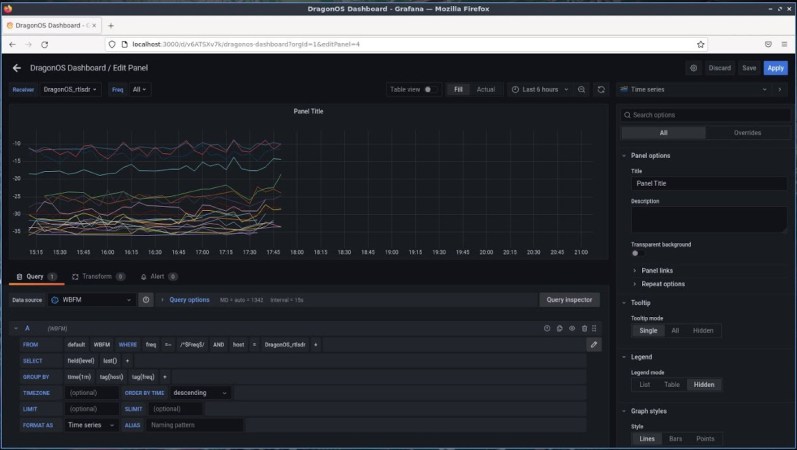
We imagine that if [Tech Minds] told us he was listening to the HF bands, we might ask him which one? His reply might just be “All of them.” That’s thanks to the RX-888 MKII SDR he reviewed which delivers a 64 MHz window on the radio spectrum. You can catch the video review, below.
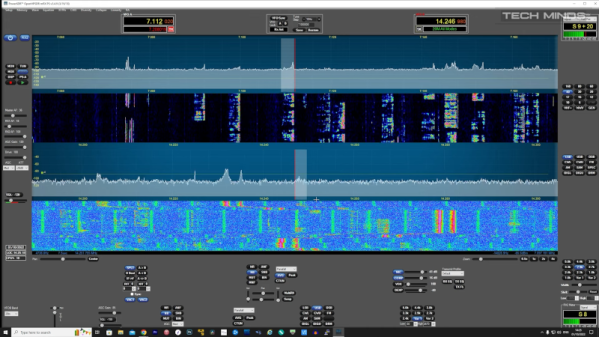
These are not especially inexpensive, but with that bandwidth and 16-bit resolution, it is worth it if you need that kind of horsepower. There is a separate input for VHF signals 64-1700 MHz where the bandwidth is only 10 MHz, but still.
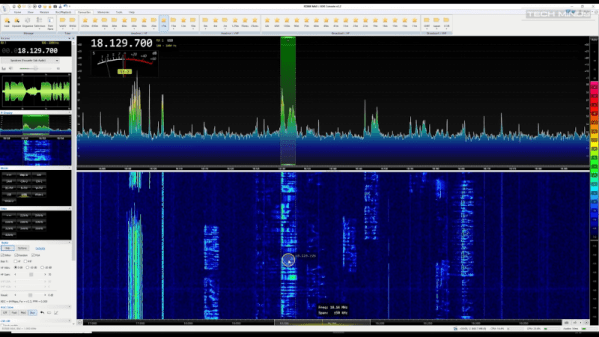
Of course, making a very wideband front end for something like this is non-trivial, so we wonder how the performance is compared to similar-priced units with less bandwidth. On the other hand, it does seem to work well enough in the video. The software used limited the test to a 32 MHz bandwidth, which is still plenty.
Speaking of software, we noticed that the developers of SatDump and SDR++ are not happy with the state of the software for the RX-888. We aren’t sure if this remains a problem, but the device seemed to work well on the video, at least.
There are many options now when it comes to higher-end SDRs. We like the Pluto for both transmitting and receiving. Of course, the RTL-SDR kind of started everything with hobby SDR, but you can’t expect that much bandwidth with one of those.