The 6502 CPU is probably the most famous of all the 8-bit processors out there, whether in the form of bare chips for homebrew computers, or as slightly modified derivative chips found in everything from the C64, the NES, and the BBC Micro. For this edition of the Hacklet, we’re taking a look at all the 6502-based builds on hackaday.io.
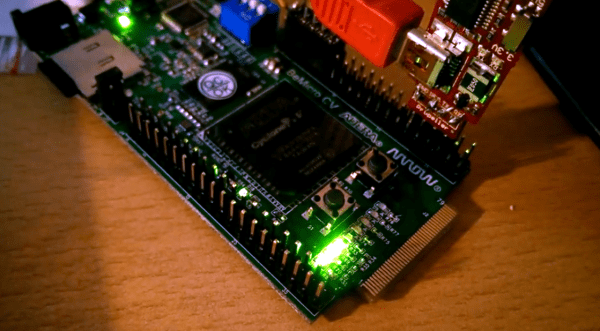
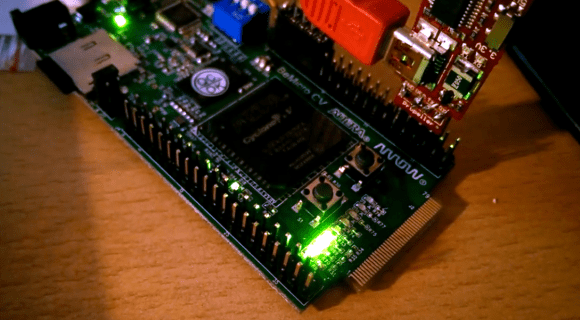
 There aren’t many transistors on a 6502, making it perfect for implementing on an FPGA. [Michael A. Morris] has an Arduino FPGA shield, and his soft-6502 project is called Cameleon. There’s a bunch of SPI Flash and FRAM on board, and the 128kB of (parallel) SRAM on the board is more than enough to handle any computational task you can throw at it.
There aren’t many transistors on a 6502, making it perfect for implementing on an FPGA. [Michael A. Morris] has an Arduino FPGA shield, and his soft-6502 project is called Cameleon. There’s a bunch of SPI Flash and FRAM on board, and the 128kB of (parallel) SRAM on the board is more than enough to handle any computational task you can throw at it.
Since the Cameleon is built on programmable logic, [Michael] thought it would be a good idea to put some of those unused opcodes to use. There are instructions for coprocessor support, and a bunch of instructions specifically designed to make the Forth implementation easier.
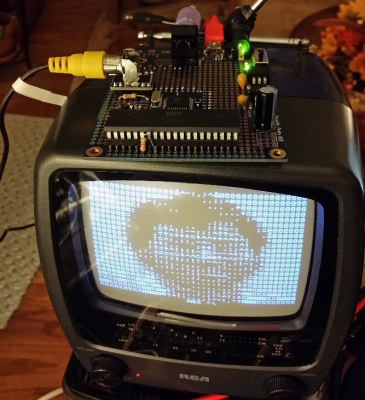
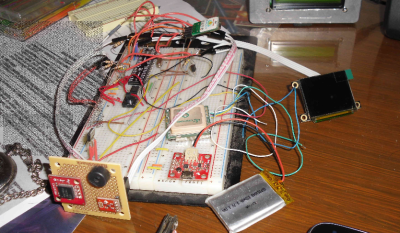
 Maybe programmable logic isn’t your thing, and you’d just like a simple computer like the Ohio Scientific or the Apple I. The L-Star is for you. That’s [Jac Goudsmit]’s build featuring a 6502, a Parallax Propeller, and little else.
Maybe programmable logic isn’t your thing, and you’d just like a simple computer like the Ohio Scientific or the Apple I. The L-Star is for you. That’s [Jac Goudsmit]’s build featuring a 6502, a Parallax Propeller, and little else.
The Parallax Propeller is a powerful (multi-core!) chip that’s easily capable of handling video out, keyboard in, and serving up the ROM and RAM of a computer. [Jac]’s build does it all beautifully, and if you’re looking for the easiest way to run code on a 6502, this is how you do it.
6502s were found in just about everything, and while poking around at the local e-waste recycler, he stumbled upon something rather interesting. The case badges screamed, “BS medical device”, but after poking around a bit, he figured out this was an MTU-130 system, a machine that was apparently the top of the line in its day.
There’s some weird stuff going on in this machine – 18-bit addressing and 80kB of RAM. So far [Eric] has managed to dump the ROM, and he’s taking a look at the floppy controller board to see if he can figure out how it’s mapped. It’s one thing to figure out what’s broken on an Apple II or C64; those are well documented machines. It’s another thing entirely to figure out a machine very few people have heard of, and we tip our hat to [Eric] and his efforts.
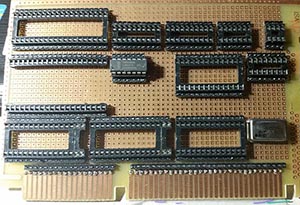
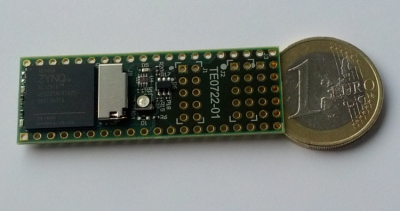
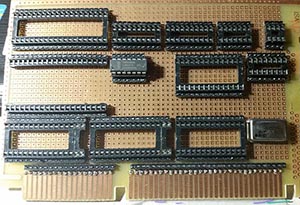 Here’s a build that both does and doesn’t have a 6502 in it. [BladeRunner]’s SheMachine is a single board computer that has a 65c816 in it. The ‘816 is an interesting beast that operates as a standard 6502 until a bit is flipped in one of its registers. After that, it has a 24-bit address space for addressing 16 Megabytes of memory, 16-bit registers, but is still completely backwards compatible with the 6502. Yes, it does have weird interleaved address pins, but we can only imagine what the world would be like if this chip came out a few years earlier…
Here’s a build that both does and doesn’t have a 6502 in it. [BladeRunner]’s SheMachine is a single board computer that has a 65c816 in it. The ‘816 is an interesting beast that operates as a standard 6502 until a bit is flipped in one of its registers. After that, it has a 24-bit address space for addressing 16 Megabytes of memory, 16-bit registers, but is still completely backwards compatible with the 6502. Yes, it does have weird interleaved address pins, but we can only imagine what the world would be like if this chip came out a few years earlier…
[BladeRunner] is designing the SheMachine with 1MB of SRAM – more than enough, really – and is mapping all the memory through a CPLD. That’s how you should do it, anyway.



 There aren’t many transistors on a 6502, making it perfect for implementing on an FPGA. [Michael A. Morris] has an Arduino FPGA shield, and his soft-6502 project
There aren’t many transistors on a 6502, making it perfect for implementing on an FPGA. [Michael A. Morris] has an Arduino FPGA shield, and his soft-6502 project  Maybe programmable logic isn’t your thing, and you’d just like a simple computer like the Ohio Scientific or the Apple I.
Maybe programmable logic isn’t your thing, and you’d just like a simple computer like the Ohio Scientific or the Apple I.