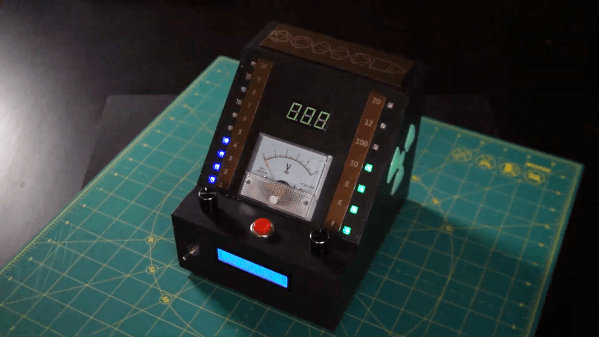
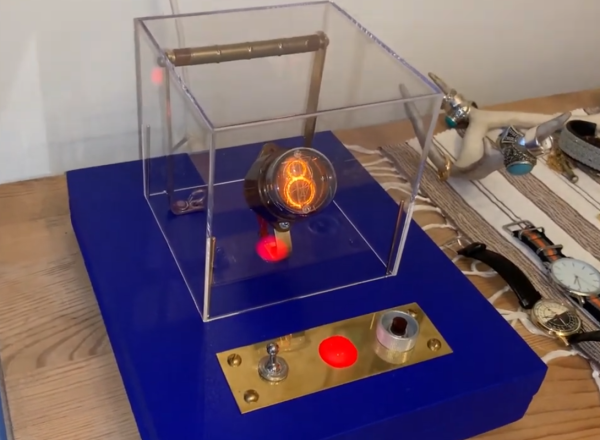
Are you making your own decisions and mainlining causality like a sucker? Why go through the agony, when you could hand over the railway switch of determinism to a machine that can decide things for you! Enter the DeDeterminator, a decision machine from [Oliver Child].

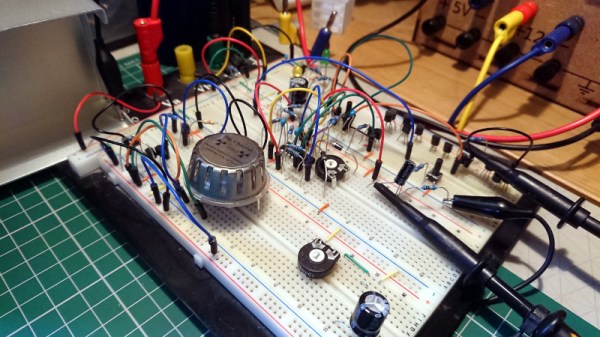
The idea is simple. At the press of a button, the DeDeterminator illuminates a bulb—indicating either yes or no. The decision for which bulb to illuminate is truly random, as it’s determined by the radioactive decay of a Americium-241 alpha particle source. A Geiger-Muller tube is used to detect alpha particles, with the timing between detections used to determine the yes-or-no output of the device.
It’s a neat concept, and it’s kind of fun knowing that your decision is both out of your hands and as random as it could possibly be. Would the universe guide you wrong? Who could possibly question the reasoning of the particles? The only rational move could be to comply with whatever directive the box hath given. Just don’t ask it to make any decisions with dangerous outcomes.
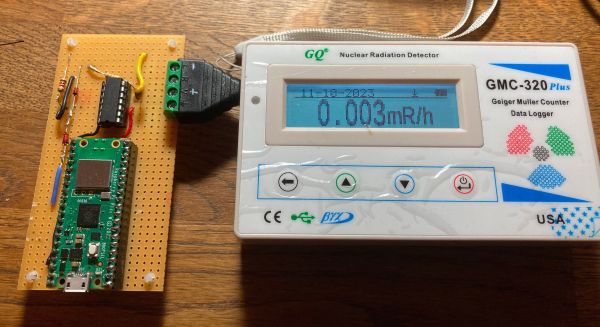
We’ve featured other projects using radioactive decay for random number generation before, though they weren’t quite as philosophically intriguing as the DeDeterminator. Mostly they’re just about cryptographic security and such, but some do deal with causality in imaginary spaces, which has its own magic about it.
Meanwhile, if you’ve untangled the quantum chains of cause and effect, or you’ve just found a way to break RSA encryption using a Pi Pico, do drop us a line, won’t you?