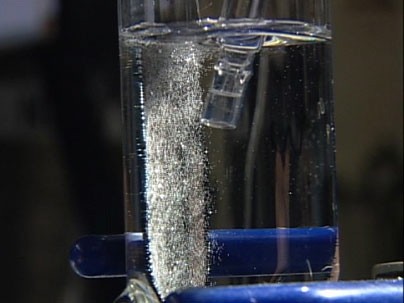
[Daniel Nocera], working with the MIT Energy Initiative, has come up with a method to easily and cheaply store energy generated from solar electricity with water. The method uses two catalysts of non-toxic and abundant metals to separate the water into both oxygen and hydrogen. These gases are then stored, and later recombined in a fuel cell to generate power. The process was inspired by photosynthesis, and helps to make sources such as solar power viable around the clock. Current storage technologies are both expensive and inefficient, so technologies like solar are only useful when the source is available. This will allow homes to cheaply and easily store power generated through solar and other technologies. While this is only part of the solution towards the current energy problem, it could go a long way towards decreasing our use of non-renewable sources. When combined with other new breakthroughs in the field, you can easily imagine more homes coming off the grid. Check out the short video after the break.
Continue reading “Breakthrough In Water Based Energy Storage”