[Alex] just bought a really nice TEAC VR-20 audio recorder, a very capable recorder perfect for recording your thoughts or just making concert bootlegs. This model was recently replaced by the Tascam DR-08 audio recorder. It’s essentially the same thing, but the Tascam unit can record at 96kHz, whereas the TEAC can only record at 48kHz. [Alex] figured out a way to upgrade his less capable but cheaper VR-20 to record at a higher bit rate with just a simple firmware hack.
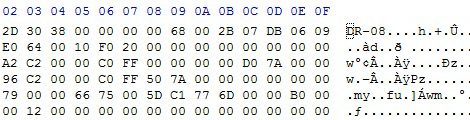
The mod began by downloading the firmware for both the TEAC VR-20 and the Tascam DR-08. Both of these sets of firmware were exactly the same size, and after downloading a hex editor, [Alex] found a huge difference in the first 20 bytes of the firmware – the portion that tells the microcontrollers what it actually is.
The solution to improving the bitrate for the TEAC VR-20 was as simple as copying the first 20 bytes from the TEAC firmware over to the first 20 bytes of the Tascam firmware. After that, it’s a simple matter of upgrading his TEAC and getting the ability to record at 96kHz.
A very, very simple hack that’s really just flipping a few bits. Not bad for a two-fold improvement in the recording capability of a handheld audio recorder.