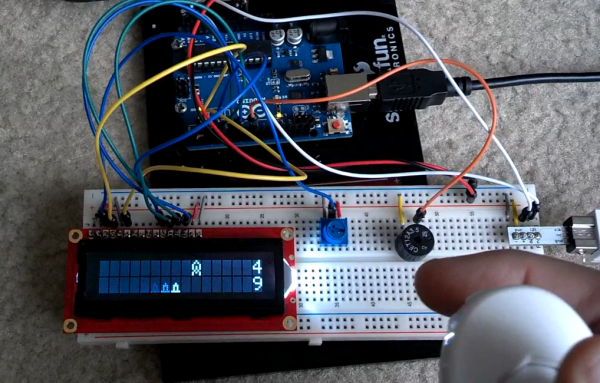
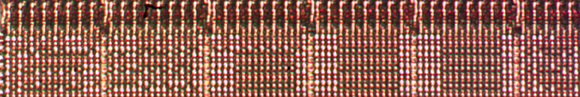
This Space Invaders game does more with less. [Rjk79] managed to make a video game using a two-line character display. The game consists of a wave of invaders on the top line, with the defender cannon on the bottom. The invader isn’t just stationary, but randomly moves to the left and the right. The image above captured a little bit of motion blur from the defender moving into position before firing on the enemy.
An Arduino board controls the 16×2 HD44780 character display. The game also includes sounds generated by the piezo buzzer seen on the breadboard. All the way to the right you can see the Wii Nunchuk breakout board which provides directional control and the firing trigger. If you want to recreate this one for yourself [Rjk79] is sharing the source code on Pastebin. There’s also a demo video found after the jump.
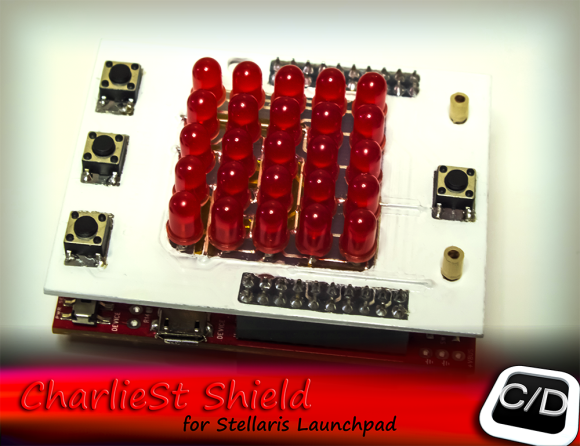
If you don’t have a character LCD on hand you might try this other Space Invaders clone that uses an 8×8 led matrix.
Continue reading “Space Invaders Played On A 16×2 Character Display”