We love re-purposed consumer gear. This project uses a cheap, discontinued cellphone gadget to create a Raspberry Pi controlled FM radio transmitter.
The Sony-Ericsson MMR-70 radio transmitter apparently used to connect to a cell phone and broadcast music. But the Walkman cellphones in question are a little bit old in the tooth, so one can buy the transmitter units for cheap on the resale market. What makes the transmitters even more interesting is that you can activate and deactivate the radio, change frequency or output power, and even send RDS station and song information.
It turns out (link in German) that the radios have an AVR ATMega32 microcontroller and a NS73 radio transmitter module, which can be entirely controlled over I2C. (Schematic here as PDF.) The units also have handy test points strewn all around. Once the test points were mapped out, one could completely ignore the on-board AVR microcontroller and control the FM transmitter module directly using the Raspberry Pi’s I2C outputs.
And that’s where [Manawyrm] stepped in. She wrote an I2C daemon for the Raspberry Pi that lets you control the FM transmitter via simple commands. All you have to do is solder up a bunch of test points, install [Manawyrm]’s software, write a batch script, and you’re on the air. For instance, this makes building a FM radio retransmitter for online streamed audio a one-day project. You can see his working example on youtube. Of course, you’ll want a web-based remote control interface to go with that.
If you’re interested in hacking along, and don’t have a Raspberry Pi application in mind, Sparkfun used to sell the NS73 radio transmitter so you can find lots of good information about the chip. We’d love to see a stand-alone broadcasting gizmo that actually utilizes the onboard AVR chip, but our hats are off to [Manawyrm] for making the Raspberry Pi version so accessible.



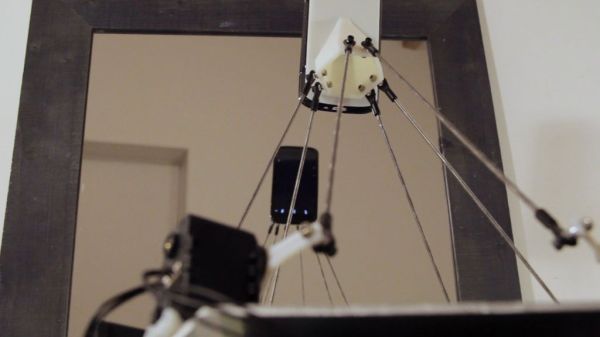
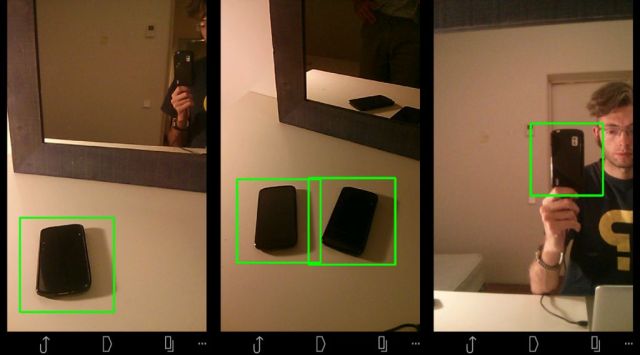 Hardware-wise, the #selfie bot is a Stewart platform made from six servo motors and a few pieces of carefully measured pushrod connected with swivel-ball-links. An android phone is mounted on the end effector which acts functionally as the robot’s face and eyes. To make it self-aware in a sense, [Ajna] and [Hersan] created their own recognition software with Open CV using a collection of sample images of various phones as reference points. As soon as the robot recognizes itself in the mirror as indicated by specific words flashing on its screen, it takes a picture, immediately uploading it to its own
Hardware-wise, the #selfie bot is a Stewart platform made from six servo motors and a few pieces of carefully measured pushrod connected with swivel-ball-links. An android phone is mounted on the end effector which acts functionally as the robot’s face and eyes. To make it self-aware in a sense, [Ajna] and [Hersan] created their own recognition software with Open CV using a collection of sample images of various phones as reference points. As soon as the robot recognizes itself in the mirror as indicated by specific words flashing on its screen, it takes a picture, immediately uploading it to its own