Robots of the future will be in the home, and ready to do whatever job we tell them to do. But they’ll need to know where they are within the house. Dead reckoning with accelerometers and gyroscopes are just a sufficient solution; what we really need is an indoor location service. For his Hackaday Prize entry, [Göran] is doing just that. He’s building a small device that will find its position with 10 cm precision, indoors.
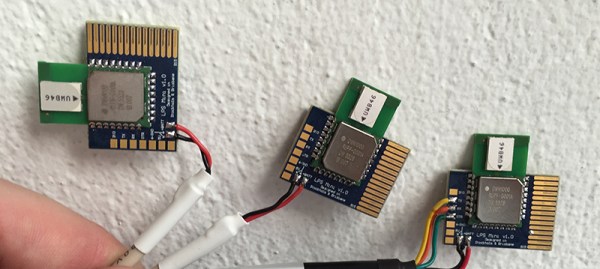
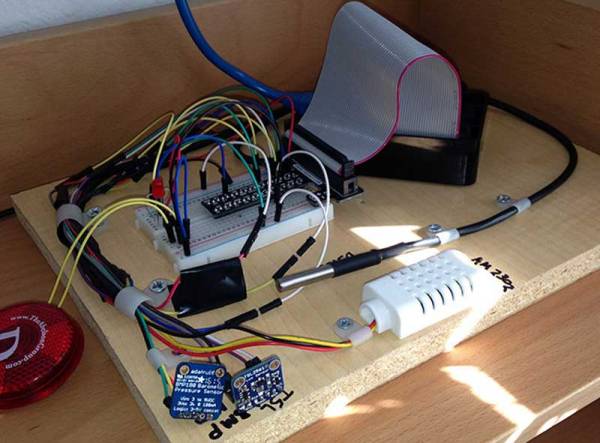
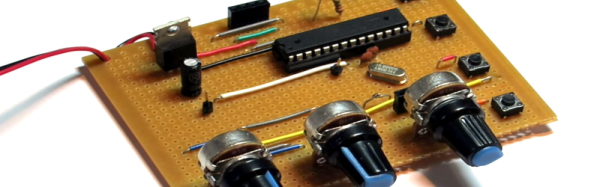
[Göran]’s LPS Mini is built around a very interesting part – the Decawave DWM100. It’s a module that uses an 802.15 radio to trilaterate the distance from several ‘anchors’ to a tag. This, by itself, gives the LPS Mini a navigation system with 10 cm precision. Even higher precision can be accomplished with an IMU gathering accelerometer, gyro, and compass data, and even further with a tiny altimeter. The result is a tiny board that knows exactly where it is.
As far as practical uses go, these LPS Mini boards were used to move beds around an art exhibit at Hayward Gallery in London. While moving beds around an art gallery doesn’t sound like a game-changing invention, think about the uses for GPS in the 1980s – no one could have imagined a chip that would tell you where you are or that could keep a quadcopter on the right heading.
You can check out [Göran]’s video for the LPS Mini below.
Continue reading “Hackaday Prize Semifinalist: Location Services For Robots”