If you’ve ever bought a suspiciously cheap Ethernet cable from an online listing, there’s a decent chance you’ve encountered Copper Clad Aluminum. Better known as CCA, it’s exactly what it sounds like—an aluminium conductor with a thin skin of copper deposited on the outside. Externally, cables made with this material look largely like any other, with perhaps the only obvious tell being that they feel somewhat lighter in the hand.
CCA is cheaper than proper copper cabling, and it conducts signals well enough to function in an Ethernet cable. And yet, it’s a prime example of corner-cutting that keeps standards bodies and professional installers up at night. But just how dangerous is this silent scourge, found lurking in so many network cabinets around the world?
Not Up To Scratch
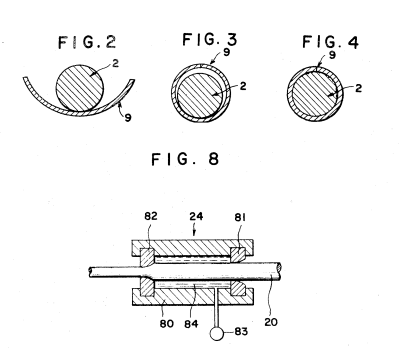
Everything you need to know about CCA is in the name—it refers to an aluminium wire with a thin copper cladding, typically applied through a die extrusion process. The reasoning behind this exploits a real physical phenomenon called the skin effect, wherein higher-frequency AC signals tend to travel along the outer surface of a conductor. The idea goes that since most of the current moves through the outer copper skin layer anyway, the less-conductive aluminium core doesn’t unduly impact the wire’s performance. Using copper-clad aluminium wiring is, in theory, desirable because aluminium is much cheaper than copper, which can really add up over long cable runs. Imagine you’re wiring a building with with hundreds of miles of Ethernet cabling, all with eight conductors each—the savings add up pretty quickly.
There’s a problem with CCA cabling in these contexts, though. Due to prevailing cabling standards, any cable made with CCA is technically not even a real Ethernet cable at all. The relevant documents are unambiguous.
ANSI/TIA-568.2-D requires conductors in Category-rated cable to be solid or stranded copper. No other materials are acceptable, and thus CCA is explicitly excluded from use in Category cable applications. A cable with CCA conductors cannot legitimately carry a Cat5e, Cat6, or any related designation under any circumstances. Similarly, ISO/IEC 11801 has the same requirement. The U.S. National Electrical Code also states that conductors in communications cables, other than coaxial cable, shall be copper. This isn’t a suggestion or a best practice; it’s the letter of the code. Anything lesser is simply not allowed. Continue reading “CCA Ethernet Cables: Not Up To Scratch, But Are They Dangerous?”