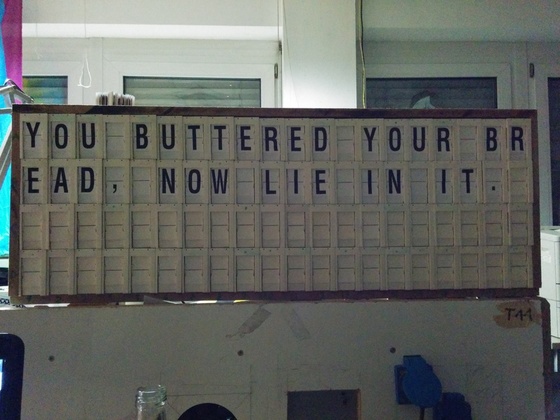
If you’ve ever encountered a rapidly spinning split-flap displays at an airport terminal, it’s hard not to stop and marvel at them in action for a few extra seconds. Because of this same fascination, [M1k3y] began restoring an old one-hundred and twenty character sign, which he outlines the process of on his blog.
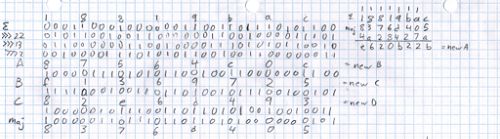
Finding documentation on this old relic turned out to be an impossibility; the producers of the model themselves didn’t even keep it off-hand any longer. In spite of that, [M1k3y] was able to determine the function of the small amount of circuitry driving the sign through process of elimination by studying the components. After nearly a year of poking at it, he happened across a video by the Trollhöhle Compute Club, demonstrating the successful use of the same display model. Luckily, they were kind enough to share their working source code. By reverse engineering the serial protocol in their example, he was able to write his own software to get the sign moving at last.
Once up and running, [M1k3y] learned that only eighty of the sign’s characters were still operable, but that is plenty to make a mesmerizing statement! Here is a video of the cycling letters in action:

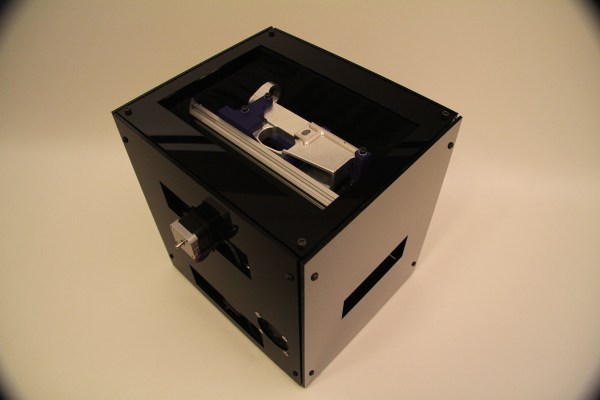
 Anyone can legally buy a barrel, trigger, stock, upper receiver, and various other parts to build an AR-15. To complete the weapon, they only need to buy an 80% lower receiver and perform the last 20% of the metal work. This work can be performed with everything from a drill press to a milling machine to hand tools. Ghost Gunner partially automates this process, making it easier and faster to complete lower receivers and build weapons.
Anyone can legally buy a barrel, trigger, stock, upper receiver, and various other parts to build an AR-15. To complete the weapon, they only need to buy an 80% lower receiver and perform the last 20% of the metal work. This work can be performed with everything from a drill press to a milling machine to hand tools. Ghost Gunner partially automates this process, making it easier and faster to complete lower receivers and build weapons.