One of the best things about open source software is that, instead of being lost to the ravages of time like older proprietary software, anyone can dust off an old open source program and bring it up to the modern era. PyOBD, a python tool for interfacing with the OBD system in modern vehicles, was in just such a state with its latest version still being written in Python 2 which hasn’t had support in over three years. [barracuda-fsh] rewrote the entire program for Python 3 and included a few other upgrades to it as well.
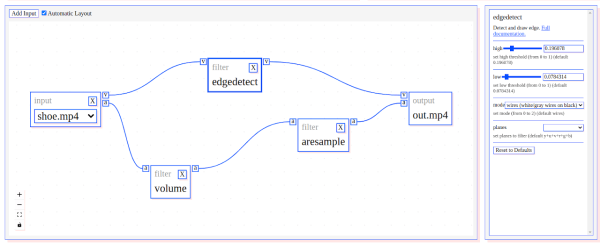
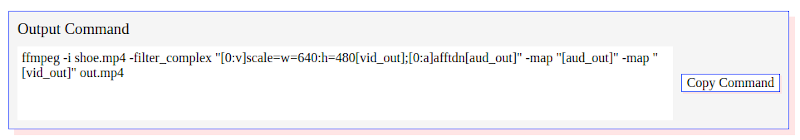
Key feature updates with this version besides being completely rewritten in Python 3 include enhanced support for OBD-II commands as well as automating the detection of the vehicle’s computer capabilities. This makes the program much more plug-and-play than it would have been in the past. PyOBD now also includes the python-OBD library for handling the actual communication with the vehicle, while PyOBD provides the GUI for configuring and visualizing the data given to it from the vehicle. An ELM327 adapter is required.
With options for Mac, Windows, or Linux, most users will be able to make use of this software package provided they have the necessary ELM327 adapter to connect to their vehicle. OBD is a great tool as passenger vehicles become increasingly computer-driven as well, but there are some concerns surrounding privacy and security in some of the latest and proposed versions of the standard.