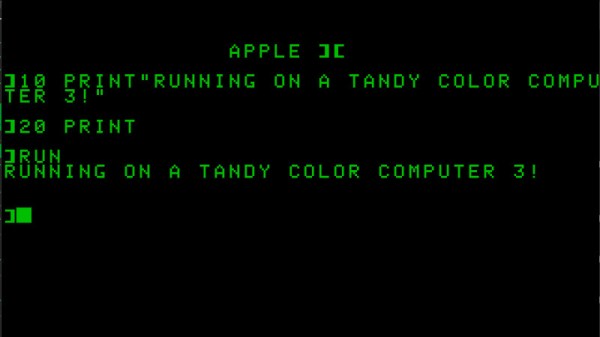
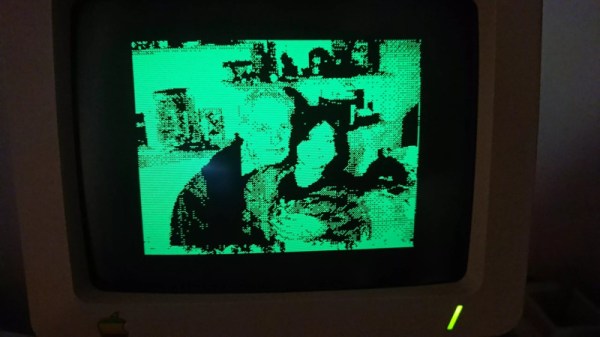
Do you remember, some years ago, when that brand-new 8086-based laptop hit the shelves? Great for PC lovers, but not so fun for those on the fruitier side of the street. Well, the same Chinese firm that brought us the Book8086 are back, this time with an ‘Apple’ Laptop that is decidedly not a MacBook– the Book II is a dual-processor Apple II clone in a laptop form factor.
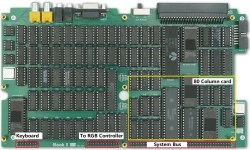
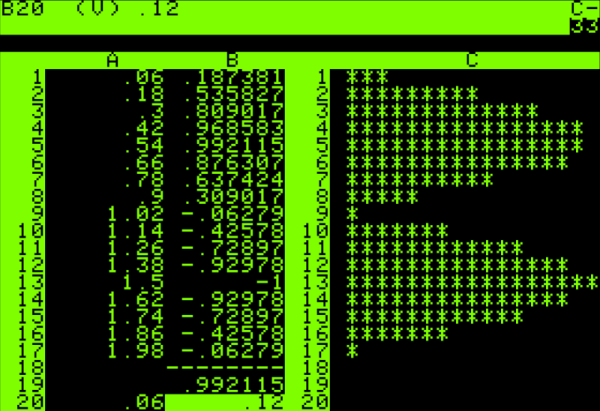
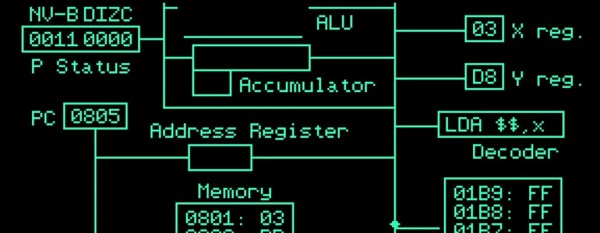
Dual processor? On an Apple II? It wasn’t that uncommon, back in the day — that’s what the Z80 softcard was, after all: a second processor that let you run CP/M and associated business applications, and this one has it built-in. It also has the 80-column video card, a second floppy controller, a printer interface, and a 16 kB ROM card for languages. That leaves two of the Apple’s expansion slots available, one of which is broken out externally on the back of the laptop, along with the printer and floppy ports.
Useful? Probably no more so than the NEC V20-based PC version. Still, those did find buyers and we have no doubt that this new laptop will, too. Especially since with the right expansion card, you might get this machine running DOS as well. Of course if you don’t feel like shelling out the quid or running an emulator, you can always roll your own Apple II on an FPGA.
Thanks to [Stephen Walters] for the tip! We usually steer clear of product announcements like this, but [Stephen] figured we’d be interested in this one since we covered the then-new retro PC versions way back in 2023.