Meshtastic has been experiencing a bit of a renaissance lately, as the off-grid, long-range radio text messaging protocol gains a ton of new users. It’s been used to create mesh networks in cities, during disasters and protests, in small groups while hiking or camping, and for search and rescue operations. Although it’s connected plenty of people together in all of these ways, [GreatScott!] wanted to put it to work connecting some computing resources instead. He has a garden shed that’s too far for WiFi, so Meshtastic was used to connect it instead.
This isn’t a project to bring broadband Internet out to the shed, though; Meshtastic is much too slow for that. All he really wanted to do here was to implement a basic alarm system that would let him know if someone had broken in. The actual alarm triggering mechanism is an LED emitter-detector pair installed in two bars, one of which sends a 12V signal out if the infrared beam from the other is broken. They’re connected to a Heltec ESP32 LoRa module which is set up to publish messages out on the Meshtastic communications channel. A second module is connected to the WiFi at the house which is communicates with his Home Assistant server.
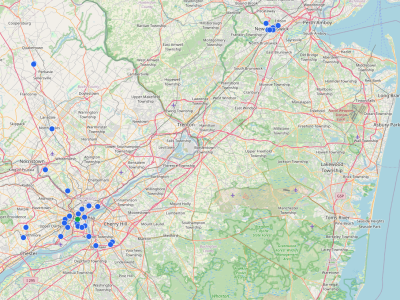
Integrating Meshtastic devices into Home Assistant can be pretty straightforward thanks to the various integrations already available, but there is some configuration to get these specific modules working as an alarm. One of the pins on the remote module had to be set up to watch the light bar, and although sending the alarm message out when this triggered worked well, the received signal never passed through to Home Assistant until [GreatScott!] switched to using the RadioLib library an an MQTT integration instead. But with perhaps more configuration than he planned for out of the way, [GreatScott!]’s alarm is up and running. Meshtastic projects often balloon into more than we had originally planned though, in more ways than one. You can follow along as our own [Tom Nardi] attempts to connect all of New Jersey with this new protocol.
Continue reading “Meshtastic Does More Than Simple Communication”