Pagers were once a great way to get a message to someone out in public; they just had to be cool enough to have one. These days, they’re mostly the preserve of doctors and a few other niche operators. [Kyle Tryon] is bringing the beeper back, though, with a custom ESP32-based build.
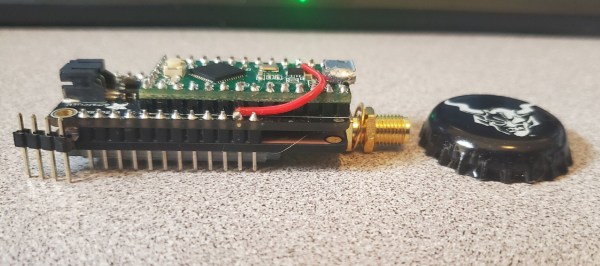
The ESP32 is a great microcontroller for this kind of project, because it’s got WiFi and Bluetooth connectivity built right in. This let [Kyle] write some straightforward code so that it could receive alerts via MQTT. In particular, it’s set up to go off whenever there’s an app or service notification fired off by the Sentry platform. For [Kyle]’s line of work, it’s effectively an on-call beeper that calls them in when a system needs immediate attention. When it goes off, it plays the ringtone of your choice—with [Kyle] making it capable of playing tunes in Nokia’s old-school RTTTL music format.
The code was simple enough, and the assembly wasn’t much harder. By starting with an Adafruit ESP32 Reverse TFT Feather, the screen and buttons were all ready to go right out of the box. [Kyle] merely had to print up a rad translucent case on a resin printer to make it look like a sweet fashionable beeper from the 90s.
It’s a fun little project that should prove useful, while also being nicely reminiscent of a technology that has largely fallen by the wayside. Continue reading “MQTT Pager Build Is Bringing Beepers Back”